Horror or Hype: The Challenge of Chemical, Biological, Radiological, and Nuclear Terrorism
Introduction
Chemical, biological, radiological and nuclear (CBRN) materials attract the attention of terrorists motivated to inflict mass casualties and create mass panic. CBRN includes a wide array of materials, some of them very difficult to acquire, although others are of a dual-use nature. Dual-use materials can be used to construct CBRN weapons, but also have licit civilian applications. Though not all CBRN weapons are weapons of mass destruction, they can still cause massive disruption and fear in a targeted society.
The goal of this paper is to evaluate the potential threat from terrorists’ use of CBRN weapons. It discusses the technical opportunities and constraints of each type of weapon and presents relevant historical and contemporary examples and case studies involving terrorist use of CBRN. The paper also assesses the contemporary threat. It examines how CBRN-related information is shared via terrorist propaganda on the internet and messaging applications, why terrorists might be motivated to use CBRN materials, and the constraints on their ambitions.

CBRN Weapons
Terrorist groups have often shown interest in developing CBRN weapons. A CBRN weapon can consist of multiple components, including the payload (CBRN agent), the munition (protects the CBRN agent), a delivery system, and a dispersal system (such as an aerosol).1 This process is termed “weaponization.” A precursor substance may also be needed for the production of some chemical and biological agents. These are usually dual-use materials that have a military and legitimate civilian application.2 The CBRN agent is the actual substance that can result in incapacitation, injury, or death for those exposed to it.
Chemical
To weaponize chemical materials, a terrorist can produce an agent using a precursor and employ an appropriate delivery mechanism. The simplest types of chemical weapons (CW) involve the release of highly volatile or gaseous chemicals such as chlorine gas or hydrogen cyanide. Certain toxic chemicals can be produced in weapons-usable quantities with less specialized equipment than is needed for other agents. Therefore, small to medium scale chemical attacks have been the most common CBRN weapon type utilized by terrorist groups. However, creating weapons of mass destruction would require considerable volumes of these types of agent.

Another option available to terrorists is the production of highly toxic, traditional chemical warfare agents (CWAs). Since 2014, there have been examples of attacks by Islamic State (IS) using sulfur mustard agents.3 However, nerve agents, such as tabun, sarin, and VX, require a more advanced level of expertise to ensure safety during the manufacturing process and maximum effectiveness when deployed.4 Terrorist groups may acquire nerve agents when unstable states lose control of chemical weapons. Although IS is believed to have gained access to nerve agents when it captured territory in Syria and Iraq in 2014,5 there is no evidence that it used these weapons.
Biological
Biological agents are found in nature and include pathogens, pests, and toxins. Pathogens are disease-causing organisms, including bacteria, viruses and fungi. Pests can include insects, worms, and plants. Biological toxins are poisonous substances produced by living organisms that can be weaponized to harm or kill humans. Biological agents are also used for legitimate research purposes, but can be subverted for illegitimate purposes.
Due to the different properties of bacteria, viruses, and toxins, they may act differently if released intentionally. Taking into account these properties, terrorists may choose simple toxins like ricin. In fact, terrorists have been successful in extracting ricin from castor plant beans.Terrorists may also resort to stealing biological agents from state-run programs.6 The potential to divert biological weapons and materials is particularly strong in countries with a history of bioweapon programs.7 There is also a concern that “insiders” or individuals with access to state-run programs could potentially provide a terrorist group with a lethal biological agent.
Radiological
Radiological agents produce casualties by emitting radiation. Radioactive material is any material that emits radiation. While radioactive materials are produced through nuclear processes, they also exist naturally, like uranium, thorium, and potassium. Radioactive materials can be used to construct radiological dispersal devices (RDDs) that spread radioactive contamination, or radiation exposure devices (REDs), also called a “hidden sealed source,” that can expose civilians to lethal or debilitating doses of radiation. Although RDDs do not produce the mass destruction characteristics of nuclear weapons such as shock waves, fires, and electro-magnetic pulses, they would have a significant psychological impact on affected populations. RDDs could be most effective when detonated in densely populated areas. REDs, constructed from partially or fully unshielded radioactive material, can be hidden from sight in a public place.8

The most vulnerable and easily obtainable radioactive materials are radiological sources housed in portable devices such as medical mobile irradiators and imaging devices.9 Potential methods of acquisition may include unauthorized transfer by a government official or a facility custodian as well as looting during coups or other types of political turmoil. Procurement can also involve licensing fraud, organized crime, vulnerable transportation links, the sale of illicitly trafficked radioactive material, and orphan radioactive sources that have been lost, stolen, or fallen outside of regulatory control.10 Within the area controlled by IS, the two potential sources of radiological material were research facilities at universities and medical devices. However, most of the material used in scientific research and medical diagnostics contains limited quantities of radioactive material and would be of little use to terrorist groups.
Nuclear
Nuclear weapons would cause the highest level of destruction, but are by far the most difficult to acquire and develop. To construct a nuclear weapon, a terrorist group would first need enough fissile material to support a sustained chain reaction. Fissile materials are any material capable of sustaining a nuclear fission chain with thermal neutrons, particularly plutonium and highly enriched uranium. The specific quantity required is determined by the weapon design. Terrorist groups may be interested in deploying an improvised nuclear device (IND). An IND incorporates fissile materials designed or constructed outside of an official government agency that may have the ability to produce a nuclear explosion.11 While terrorist groups may judge it easier to obtain fissile material and construct their own weapon, fabricating fissile material from raw products would demand prolonged engagement in either the enrichment of uranium or the chemical separation of plutonium. Experts believe that these processes are too complex, costly, and detectable for any currently known terrorist organization to attempt.12
Terrorist Use of CBRN Materials
Islamic State
After 2014, IS controlled considerable territory, had access to precursor chemicals, laboratory equipment, and technical expertise. These advantages gave IS the opportunity to develop a CW capability. IS reportedly deployed chlorine, sulfur mustard, phosphine, and other toxic industrial chemicals such as vinyltrichlorosilane.13 Its forces employed chemicals in both offensive and defensive operations. IS utilized chemical weapons in up to thirty-seven separate attacks in Syria and Iraq.14 In total, there were at least twenty instances of the use of chlorine by IS. The group was also reported to have used sulfur mustard chemical agent in August and September 2015. Another set of attacks took place in February and March 2016.15 In 2017, IS operatives allegedly directed the construction of a chemical dispersal device in Sydney, Australia. An individual identified by the Australian Federal Police as a senior IS figure in Syria allegedly instructed the Australian suspects in the construction of a device that could disperse hydrogen sulfide, a toxic industrial chemical.16
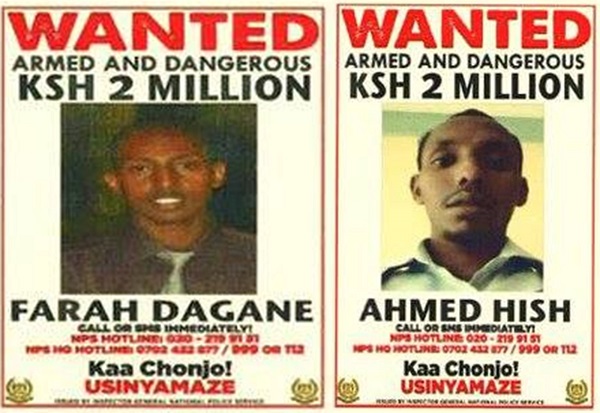
IS also attempted to use biological weapons. In May 2016, Kenyan and Ugandan law enforcement agencies arrested individuals linked to IS who were planning a terrorist attack using anthrax.17 In June 2018 in Cologne, Germany, law enforcement agencies arrested a Tunisian national named Sief Allah H., who had been building an explosive device containing ricin. The suspect had communicated with two IS members based in North Africa or Syria via the encrypted messaging application Telegram since the fall of 2017.18 They allegedly gave him advice on ricin production and information on how to build an explosive device for its dispersal.19 During the 2014 Ebola crisis in Africa, there were even reports that IS might attempt to use Ebola-infected individuals as delivery systems for the virus.20
IS has also voiced an interest in radiological and nuclear weapons. In 2014, reports stated that the group had seized eighty-eight pounds of Iraqi uranium from Mosul University. However, the materials were of low-grade and did not pose a security threat, as they would not have been suitable for an IND, RDD, or RED.21 In 2015, IS’s Dabiq publication claimed that the group had the ability to acquire and smuggle a state-built nuclear weapon across the southern border of the United States, although this claim was assessed to have no credibility.22
Al Qaeda
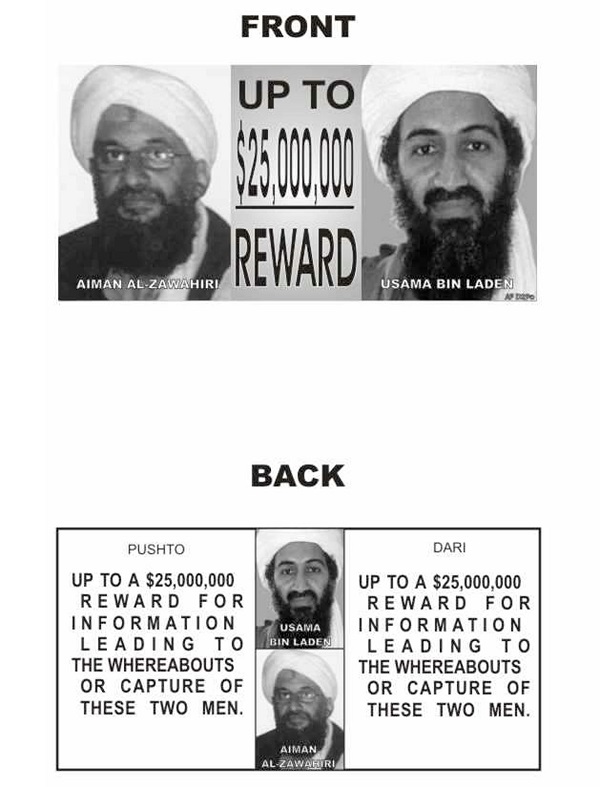
Al Qaeda had the most ambitious and persistent program to develop CBRN weapons. The group tried to obtain highly enriched uranium on several occasions23 and considered the sabotage of vulnerable nuclear power plants.24 In November 2001, Osama bin Laden even declared that al Qaeda possessed nuclear weapons as a deterrent against a U.S. nuclear attack. In the same interview, Ayman Zawahiri, another senior official of the group, said that al Qaeda had obtained nuclear weapons through the Asian nuclear black market.25 The group also made it clear that they wanted a radiological weapon.26 Although little came of this ambition, Jose Padilla, who claimed to be part of al Qaeda, was arrested in 2002 in Chicago on suspicion that he planned to carry out an attack using a RDD.27 Finally, in 2006, Dhiren Barot, an al Qaeda supporter, was convicted in the UK for his involvement in a radiological weapon plot against U.S. and British targets.28
Allegedly, al Qaeda undertook the development of chemical weapons, but abandoned the program after several failures.29 Al Qaeda had considered using cyanide along with explosives during the 1993 World Trade Center Bombing in New York.30 In March 2003, al Qaeda also planned an attack on New York’s subway system deploying cyanogen gas from a device. The group called the device mubtakkar or “invention.” However, at the last moment a key al Qaeda leader reportedly called off the attack.31
Right-wing Terrorists in the U.S.
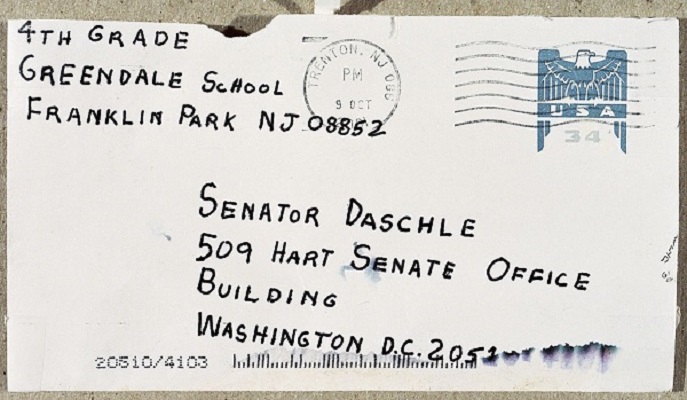
Right-wing CBRN terrorism is rare, but examples when they occur often involve middle-aged and comparatively well-educated male perpetrators, mostly motivated by non-religious forms of far-right ideology, such as neo-Nazism or white supremacism.32 In April 2003, the FBI arrested right-wing extremists William J. Krar, Judith Bruey, and Edward Feltus. Law enforcement officers found chemicals, including nitric and acetic acids along with sodium cyanide, as well as instructions on how to produce chemical weapons at a storage unit that they had rented.33 More notably, in 2001, Bruce E. Ivins, a U.S. Army civilian research scientist, had mailed letters containing a highly virulent and sophisticated form of anthrax to media offices and the offices of two U.S. senators. Five people died, seventeen people became gravely ill, the mail service stopped, and one of the Senate office buildings were shut down for fear of additional attacks.34 Ivins committed suicide before an ideological motivation could be established.
According to leading scholar of terrorism, Audrey Ruth Cronin, U.S. extremist groups, such as the Minnesota Patriots Council, have shown an interest in weapons such as “ricin, plague, anthrax, hydrogen cyanide, sarin, and other agents.”35 There is evidence that the U.S. Patriot Movement and affiliated organizations intended to use chemical weapons, including cyanide and sarin, but have apparently lacked the ability or opportunity to acquire them.36 In May 2017, a member of the right-wing neo-Nazi group called “Atomwaffen” was arrested in Tampa, Florida in possession of explosives and two radiological materials, thorium and americium.37 These materials could have been used to construct a RDD but, as with so many other plots of this kind, the probability of success would have been low.
Aum Shinrikyo
Aum Shinrikyo was a Japanese doomsday cult led by Shoko Asahara. Reportedly, the group spent over twenty million dollars over a four-year period trying to develop its chemical and biological weapons capabilities.38 Throughout the early 1990s, Aum Shinrikyo carried out at least twelve chemical attacks (using sarin, VX, phosgene, and hydrogen cyanide).39 The highest number of casualties were reported after the group’s nerve gas attack on the Tokyo subway in 1995. Although the group used low quality sarin with a poor dissemination method, the attack killed thirteen people and injured several hundred others.40
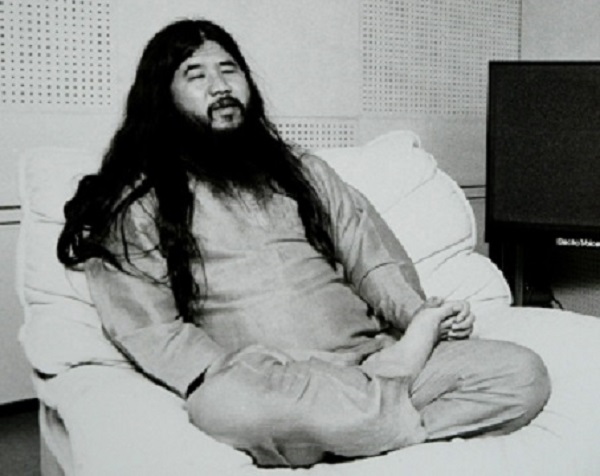
From 1990 to 1995, Aum Shinrikyo experimented with biological agents such as anthrax, botulinum toxin, cholera, Q fever, and even Ebola, but was unsuccessful due to ineffective delivery mechanisms and nonvirulent strains.41 In 1993, the group reportedly sent its representatives to an Ebola outbreak in Zaire (now the Democratic Republic of Congo) in an attempt to acquire samples of the disease for use in their bioweapons program. In all, Aum Shinrikyo has been accused of carrying out at least six different biological attacks using both anthrax and botulinum toxin.42
The group also attempted to acquire nuclear weapons and reportedly had a budget of about fifteen million dollars.43 No reports indicate that the group had any success in this endeavor. The uranium acquisition project involved buying a sheep ranch in Australia in 1993 that had known deposits of uranium ore and attempting to import mining equipment. The program was abandoned when Australian customs agents refused to allow the mining equipment into the country.44 The relative failure of Aum Shinrikyo’s efforts to weaponized CBRN materials, despite extensive resources and efforts, illustrates the perennial problems that terrorists groups face when they seek to employ such weapons in support of their campaigns.
The Liberation Tigers of Tamil Eelam (LTTE)
The LTTE was a secessionist Tamil group that sought an independent Tamil state in the north and east of Sri Lanka. They eventually suffered military defeat by Sri Lankan government forces in 2009. In 1990, LTTE used chlorine against the Sri Lankan Army. They moved drums of chlorine from a paper factory, allowing the prevailing winds to carry the gas towards their adversary. An estimated sixty Sri Lankan military personnel suffered injuries from the gas release.45 Some of the Sri Lankan officers created makeshift masks to protect themselves, but the wind shifted and moved some of the gas towards LTTE and Tamil civilians. Due to protests from the Tamil community, which condemned the LTTE’s use of chemical weapons, the group made no further attempts to use CBRN weapons.46

Rajneeshees
The Rajneeshees were a cult that followed the teaching of Indian mystic Bagwan Shree Rajneesh. The cult had a commune in Oregon that it wanted to expand, but citizens and local officials were opposed to the idea. In 1984, the cult developed a plan to decrease voter turnout in the general population by carrying out the first recorded U.S. bio-terror attack. This would have allowed them to elect cult members who would then approve legislation to allow for the desired expansion. The cult had a number of medical personnel among their members. These specialists cultivated salmonella, which they placed in the salad bars of local restaurants. At least 751 people fell ill from the attack, but none died.47 The attack was not discovered until a year later when a defector from the group informed the authorities.
The Emerging Threat
Motivations
For terrorists, one of the major attractions of CBRN weapons is their psychological impact on targeted societies.48 There are also operational, political, and theological motivations for terrorists to use CBRN weapons. For example, a group’s use of a CBRN weapon could be a demonstration of its relative power. Media coverage of the incident might also stimulate recruitment and fundraising for the terrorist group as well as advertise the terrorists’ ideology. The use of CBRN weapons can also be a demonstration of a group’s resolve. A successful attack would likely have a significant economic impact on the target country as well as affect the country’s infrastructure and even its political system.49 In addition, a CBRN incident would represent a difficult challenge for first responders and would likely damage public perception of the target government’s competence in a crisis.50
IS used CW for operational purposes, but its activities were almost entirely confined to battlefields and their immediate environs. However, the group’s use of CW arguably promoted its image as a formidable terrorist entity and spread fear among the wider public through media coverage of the attacks. IS was allegedly directly engaged in terrorist plots in Australia and Germany, where chemical and biological weapons were constructed. If successful, these attacks could have spread fear in Western publics and demonstrated the competence and reach of the group.
In 2003, a Saudi cleric, Nasir bin Hamd al-Fadh, issued a fatwā in which he argued that as the U.S. had killed millions of Muslims, an al Qaeda attack that killed millions of Americans would be justified and permissible.51 In 2012, an Inspire magazine article posthumously published a quote from Anwar al-Awlaki, a key leader of al Qaeda in the Arabian Peninsula that stated, “The use of poisons of chemicals and biological weapons against population centers is allowed and strongly recommended due to the effect on the enemy.”52 Both examples may represent theological motivations for terrorists to use CBRN weapons.
Information and Propaganda on Social Media
Online propaganda messages may motivate would-be terrorists to use CBRN materials. Tutorials on how to construct CBRN weapons are often posted online, especially in certain social media platforms. Terrorist organizations, via their magazines, news outlets, or messaging applications, promote and instruct would-be terrorists in how to manufacture CBRN devices.
In May 2018, French counterterrorism police arrested two suspects in Paris. According to the official statement, the two men were arrested for “preparing to commit an attack, with either explosives or ricin.” According to the authorities, the suspects had communicated via the messaging application Telegram and had tutorials that demonstrated how to make ricin-based poisons.53
As mentioned above, German police arrested Sief Allah H. in June 2018 on suspicion of making ricin. Three mobile phones were confiscated during the investigation and several files containing bomb-making manuals were stored on one of the devices.54 Amid the content was IS jihadi propaganda. One of the online videos was allegedly the same found during an investigation against the two suspects arrested in France.55
In another case, in August 2017, Indonesian police arrested five suspects who were members of the Jamaah Ansharut Daulah (JAD), an IS-linked group. The suspects were trying to transform low-grade radioactive thorium 232 into uranium 233, as instructed by Nuclear for Dummies, a forty-seven page Indonesian-language bomb manual written by JAD leader Bahrun Naim.56 This was a work of fantasy, as the required transformation needed a nuclear reactor and therefore was clearly an impossible task for terrorists working in a domestic environment. Nevertheless, the case highlights continued efforts by jihadist terrorists to acquire a device of mass destruction, as claimed on IS’s social media.

An increased opportunity to experiment with CBRN materials elevates the chances that terrorists could be successful in constructing a viable device. In 2018, an IS-linked group launched a campaign promoting the use of biological weapons and released instructions for producing homemade weapons. In 2017, the Furat Wilayah channel released several documents in English from the “Knights of Lone Jihad.” Several CBRN scenarios involving food and water contamination were advocated as possible terrorist tactics.57 As the instructions were simple, terrorists with no initial scientific knowledge or experience could attempt to use them. Earlier in May 2016, jihadists had published a detailed online tutorial to produce ricin toxin. Anders Breivik’s manifesto, published prior to his attacks in Norway in 2011, also encouraged sympathizers to develop anthrax, ricin, and liquid nicotine.58 This information could motivate other right wing terrorists to attempt to manufacture CBRN weapons, especially as Breivik has become something of a cult figure for many right-wing extremists.
Constraints
Various theories have attempted to explain why terrorists have not successfully mounted a major CBRN attack. One explanation is that state policies to thwart such attacks have so far been successful. Individual states and the international community have made strenuous efforts to impede terrorists’ abilities to communicate, fundraise, and coordinate activities, thus diminishing their opportunities for success.
Another argument is that terrorist groups are satisfied with the impact they can achieve through conventional means and tactics, such as firearms, knives, automobiles, or improvised explosive devices (IEDs), and therefore have little interest in pursuing weaponized CBRN. During 2018, the media reported 1,329 IED incidents. As a result, 3,159 security force personnel and 2,833 civilians were killed. Total casualties numbered 12,525.59 While conventional weapons remain effective, there is arguably little incentive for terrorists groups to tackle the significant challenges required to acquire, weaponize, and deliver CBRN.
Certain terrorist groups may be unwilling to commit mass casualty attacks. The LTTE’s use of chemical weapons was constrained by the negative response from their constituents. Terrorists may be concerned that the use of CBRN weapons could actually deter fundraising and recruitment rather than encourage it. These factors may indicate that only a limited number of terrorist groups would be willing to use CBRN, even if they had the capability.60
Terrorists thus far appear to lack the ability to develop and deploy CBRN weapons of truly mass impact. Certainly, there are numerous hurdles that terrorist groups have to overcome to carry out a large-scale attack using CBRN weapons. Regardless of weapon category, the development of CBRN weapons of mass effect requires significant expertise and resources. Diverse knowledge and skill sets are needed to acquire the necessary agent, to produce an agent of sufficient quantity and quality, and to store, transport, and disseminate it. Along with technical expertise, a CBRN weapons program needs significant funding as well as a secure manufacturing location. Some terrorist organizations, including al Qaeda, Aum Shinrikyo, and IS, have demonstrated the ability to obtain the necessary funding and security to develop limited CBRN capabilities. However, it is a challenge for groups to maintain security for an extended period without interference or detection. Due to fears of a government raid, Aum Shinrikyo had to dismantle its CBRN programs several times, thus hindering progress in weapons production.61
There are also weapon-specific constraints. For example, chemicals such as hydrogen cyanide, sarin, and their precursors are highly corrosive and require storage in highly controlled environments. Due to their corrosive nature, the agents will immediately begin to eat away at rubber seals and the container itself, making leaks inevitable.62 Because of these constraints, if terrorist groups developed chemical agents, they would likely have to deploy them immediately and most probably within close geographic proximity to the location of their manufacture.
There are also a number of complications for terrorists seeking to manufacture biological agents. These include but are not limited to obtaining the correct microorganism, procuring the right equipment, avoiding contamination, and ensuring virulence during weaponization.63 To achieve mass casualties by using biological agents, a terrorist also needs to transport or smuggle an agent to the target without compromising the pathogenicity and virulence of the microbe.64
In the case of radiological materials, a terrorist will need to overcome challenges related to safe handling and have the knowledge to identify the correct amounts and types of explosives for dispersal over a targeted area. A terrorist would also need to have the skills to fabricate the required physical form of the radioactive source to ensure effective dispersal of the material.65
Alliances
As discussed above, there are significant hurdles for terrorists to surmount in order to construct a viable CBRN weapon. These factors include access to scientists, engineers, materials, infrastructure, money, information, and lines of communication. Rarely could a terrorist group, let alone a lone-actor, have access to all of these resources. Therefore, terrorists may look for alliances with criminal groups to fill their capacity gaps.66 A recent CTC Sentinel article argues that a network that facilitates the development of IEDs is similar to the elements that facilitate the proliferation of WMD.67 During the twelve month period between September 1, 2017 and August 31, 2018, there were approximately 16,300 IED incidents worldwide, not including those within the U.S.68 While conventional IED facilitation networks function more effectively than those for CBRN, there is a possibility that “profit-minded suppliers”69 would consider CBRN weapons’ facilitation if there were relatively low additional risk.70 Jihadists have looked into buying HEU on the black market, even though it would cost tens of millions of dollars. In 2015, the FBI and Moldovan police interdicted several attempts by criminals to sell radioactive material to extremists in the Middle East.71 One case involved a scheme to sell HEU at forty million dollars per kilo.72 In March 2019, the State Security Service of Georgia detained two members of a criminal group allegedly planning to sell over forty grams of the nuclear material uranium-238 for $2.8 million.73 In April 2016, the same agency arrested six people who were allegedly planning to sell uranium-238 for $200 million.74 However, it is not known whether many transnational criminal organizations would be willing to engage directly in WMD proliferation to facilitate terrorism.
How Dangerous is the CBRN Threat?
Taking into account IS’s current situation, arguably the most likely CBRN threat from the group would involve returning or relocating foreign fighters, especially as some experts involved in IS’s CW program are likely to have left Syria and Iraq for safer places. Although IS abandoned the use of CW on the battlefield, it retains the motivation and probably the expertise to construct at least a rudimentary chemical device.
From the records of 4,100 captured IS personnel, it is apparent that 109 members have some sort of background in science, technology, engineering, and mathematics.75 Publicly available information on individuals killed or detained by the U.S. coalition suggests that IS assembled at least one dedicated team of technical experts to develop its CW program, using improvised laboratories in Mosul.76 Available reporting suggests that those experts, who were from Russia and Southeast Asian countries and had relevant technical expertise, had migrated to the caliphate. Many had been involved in CW research for other jihadi groups prior to the establishment of IS. Arguably, the threat from these individuals remains real.77 Furthermore, recent cases in Australia and Germany demonstrated IS’s intent and capacity to remotely supervise the construction of deadly weapons targeting western countries. IS’s actions to recruit, radicalize, and instruct would-be terrorists via the internet or messaging applications will likely continue.
As regards biological weapons, terrorists may employ biological engineering in addition to simple toxins like ricin. The technology is advancing rapidly as knowledge becomes more widespread. For example, terrorists could eventually take advantage of the expertise in gene editing, which could then be used to unleash diseases and pathogens.78

Terrorists may also attempt to construct devices with radiological materials, primarily RDDs. Its design is much simpler than a true nuclear device, although its manufacture exposes operators to a potentially lethal radioactive hazard. Though there is no evidence that terrorists have acquired the necessary radiological materials, there are incidents of their trafficking and malicious use. According to the International Atomic Energy Agency Incident and Trafficking Database, out of 3,497 reported incidents since December 2018, 285 cases involved a confirmed or likely act of trafficking or malicious use of nuclear or other radioactive materials.79 According to another source, “between 1990 and 2010, there were close to 400 incidents of radiological materials that fell out of regulatory control. Since 2010, these incidents have doubled.”80 Both sources demonstrate that the control of nuclear and radiological material remains a challenge for the international community and more effective measures need to be taken to counter terrorists’ access to these materials.
IS raised the possibility of purchasing radiological material and claimed in May 2015 “it could buy a nuclear weapon… within the coming year.”81 At that time, IS had the funds to buy the twenty kilograms they needed for a radiological device that could yield two kilotons of energy.82 Incidents using radioactive sources have occurred in the EU, despite strict regulations and control mechanisms. In November 2016, for example, several institutions in Slovakia, including the Ministry of Justice, district courts, and a regional police office received suspicious envelopes containing the radioactive material americium-241. The Slovak authorities investigated the case as an act of terrorism.83 In December 2013, a cargo truck carrying hospital equipment containing cobalt-60 was stolen from a gas station in Mexico.84 Though the case was not terrorism related, it highlights vulnerabilities that could be exploited by terrorists to acquire dangerous materials.
Nuclear power plants and nuclear weapon facilities remain potential targets. In Belgium in 2015, during a house search of a suspect linked to the November Paris attacks, a video was found containing surveillance footage of a senior executive of a nuclear research site.85 However, there is no evidence that the terrorist’s intention was to actually steal nuclear material.
Terrorists may use the internet, particularly the Darknet, for the procurement of various types of materials. In 2015, biological toxins such as abrin and ricin were reportedly sold on the Darknet using cryptocurrencies.86 The same year, a man who tried to buy ricin from the Darknet was arrested in the UK.87 In 2014, at least two individuals from two different EU member states purchased the biological toxin abrin from a vendor located in the U.S. through a Darknet marketplace.88
In early 2017, IS began using unmanned aerial vehicles (UAVs), primarily from the Phantom series of quadcopters, to drop IEDs on enemy troop concentrations up to several kilometers behind the front line. Although it is not clear whether IS successfully used UAVs to deliver chlorine gas,89 the use of UAVs to mount CBRN attacks may be a significant challenge in the future, if terrorists can overcome the technical difficulties involved.
Finally, terrorist groups might also use hoax CBRN devices or threaten to use weapons that they do not actually possess.90 Terrorists would use such ploys to spread fear and disruption, cause the public to criticize and mistrust the targeted government, and force the latter to expend scarce resources to deal with the “threat.” Terrorists may also employ a hoax device to study a government’s response in preparation for a real attack with a viable CBRN device.
Conclusions
Terrorists have demonstrated their willingness to use CBRN devices. They will likely seek to advance their knowledge and capabilities to construct viable CBRN weapons. Development of new technologies and access to commercial off-the-shelf applications further increases the terrorists’ chances of success.
Foreign fighters with expertise and experience in constructing CBRN weapons have been living in Syria and Iraq. Their attempts to relocate or return to their home countries potentially poses an elevated CBRN threat as they could instruct other would-be terrorists to construct viable devices. Most likely, they will focus on the use of dual-use chemicals or toxins, like ricin, to conduct small-scale CBRN attacks. It is highly probable that terrorists will use the internet, particularly Darknet, for the procurement of components for these devices.
Despite losing its territory in the Middle East, IS retains sufficient funds to acquire radiological or nuclear materials. However, funding is not the major obstacle; rather the availability of materials and the identification of a willing seller remain more challenging for prospective CBRN terrorists.
Examples cited in this paper have illustrated how effectively terrorists are sharing information using the internet and messaging applications. For the reasons discussed in this paper, the overall threat of CBRN terrorism remains small, but terrorists can be expected to continue their efforts to construct the CBRN devices of the kind that feature prominently in terrorist on-line propaganda.
Robust countermeasures programs will assist governments to tackle the challenges of CBRN terrorism. While terrorists need to overcome several major hurdles to construct CBRN devices, preventing them from acquiring the materials to produce these devices remains the most critical step. An analysis of countermeasures is outside the scope of this paper, but outreach programs, public-private cooperation, and engagement with international organizations will remain crucial to elevate governments’ preparedness and response capabilities.
Although the media has hyped CBRN events, terrorists face significant difficulties in acquiring, weaponizing, and delivering weapons of truly mass effect. Nonetheless, the prospect of CBRN use triggers primal fear. Even a relatively small scale, successful incident could create a level of horror in the target population quite unlike that from a conventional terrorist attack. This alone provides a motive for terrorists to persist in their efforts to develop effective CBRN weapons.
For Academic Citation
Lasha Giorgidze and James K. Wither, “Horror or Hype: The Challenge of Chemical, Biological, Radiological, and Nuclear Terrorism,” Marshall Center Occasional Paper, no. 32, December 2019, https://www.marshallcenter.org/en/publications/occasional-papers/horror-or-hype-challenge-chemical-biological-radiological-and-nuclear-terrorism-0.
Notes
1 Marie-Helen Maras and Michelle D. Miranda, “The Weaponization of Ebola: A New Risk in the Wake of an Outbreak?” Comparative Strategy 35, no. 1 (2016): 72-79 and Multiservice Tactics, Techniques, and Procedures for Treatment of Chemical Agent Casualties and Conventional Military Chemical Injuries, (Washington, D.C.: Army, Marine Corps, Navy, Air Force, 2007).
2 Aaron K. Martin, “Innovation, Dual Use, and Security: Managing the Risks of Emerging Biological and Chemical Weapons,” ed. Jonathan B. Tucker, Science and Public Policy 40, no. 6 (2013): 824-26.
3 Associated Press in Iraq, “Islamic State Used Chemical Weapons against Peshmerga, Kurds Say,” The Guardian, March 14, 2015, https://www.theguardian.com/world/2015/mar/14/islamic-state-isis-used-chemical-weapons-peshmerga-kurdsand “Islamic State ‘used mustard gas’ against peshmerga,” BBC News, October 07, 2015, https://www.bbc.com/news/world-middle-east-34471237.
4 Stephanie E. Meulenbelt and Maarten S. Nieuwenhuizen, “Non-State actors’ pursuit of CBRN weapons: From motivation to potential humanitarian consequences,” International Review of the Red Cross 97, no. 899 (September 2015): 831-858.
5 Gary Ackerman and Michelle Jacome, “WMD Terrorism: The Once and Future Threat,” PRISM 7, no. 3 (May 15, 2018): 23-36, https://cco.ndu.edu/News/Article/1507339/wmd-terrorism-the-once-and-future-threat.
6 Cheryl Loeb, “Jihadists and Biological and Toxin Weapons,” in Jihadists and Weapons of Mass Destruction, eds. Gary Ackerman and Jeremy Tamsett (Boca Raton: CRC Press, 2009), 153-172.
7 Jonathan B. Tucker, “Preventing the Misuse of Pathogens: The Need for Global Biosecurity Standards,” Arms Control Today 33, no. 5 (2003): 3-10.
8 INTERPOL, Radiological and Nuclear Terrorism Guidance Manual, 2015, 60.
9 David C. Trimble, Nuclear Nonproliferation: Additional Actions Needed to Increase the Security of U.S. Industrial Radiological Sources, GAO-14-681T (Washington D. C., June 12, 2014), 1-3.
10 Charles D. Ferguson, William C. Potter, and Amy Sands, The Four Faces of Nuclear Terrorism, (New York: Routledge, 2005), 271-278.
11 Interpol, Radiological and Nuclear Terrorism Guidance Manual, 2015, 98.
12 Ackerman and Jacome, “WMD Terrorism,” 25.
13 Ibid.
14 Markus K. Binder, Jillian M. Quigley, and Herbert F. Tinsley, “Islamic State Chemical Weapons: A Case Contained by Its Context?” CTC Sentinel 11, no. 3 (March 2018): 27-31, https://ctc.usma.edu/islamic-state-chemical-weapons-case-contained-context/.
15 Ibid.
16 Andrew Zammit, “New Developments in the Islamic State’s External Operations: The 2017 Sydney Plane Plot,” CTC Sentinel 10, no. 9 (October 2017): 13-18, https://ctc.usma.edu/new-developments-in-the-islamic-states-external-operations-the-2017-sydney-plane-plot/ and Rachel Olding, “Khaled Merhi pleads not guilty to weapons charge after Sydney ‘bomb plot’ raid,” The Sydney Morning Herald, August 24, 2017, https://www.smh.com.au/national/nsw/khaled-merhi-pleads-not-guilty-to-weapons-charge-after-sydney-bomb-plot-raid-20170824-gy2wwm.html. This development followed a failed attempt to down an Emirati airliner using an improvised explosive device.
17 Alexander Smith, “Kenya Police Say They Foiled ISIS-Linked Plot to Unleash Anthrax Attack,” NBC News, May 4, 2016, https://www.nbcnews.com/news/world/kenya-police-say-they-foiled-isis-linked-plot-unleash-anthrax-n567721.
18 Der Generalbundesanwalt Beim Bundesgerichtshof: Pressemitteilung, July 24, 2018, https://www.generalbundesanwalt.de/de/showpress.php?themenid=20&newsid=783, accessed December 2019.
19 Der Generalbundesanwalt Beim Bundesgerichtshof: Pressemitteilung, August 03, 2018, https://www.generalbundesanwalt.de/de/showpress.php?heftnr=788&newsid=788, accessed December 2019.
20 Jamie Doward, “Top-secret military warning on Ebola biological weapon terror threat,” The Guardian, February 21, 2015, https://www.theguardian.com/uk-news/2015/feb/21/top-secret-ebola-biological-weapon-terror-warning-al-qaida-isis.
21 Alexander Smith, “Nuclear Experts Play Down Threat of Uranium Stolen by ISIS,” NBC News July 10, 2014, https://www.nbcnews.com/storyline/iraq-turmoil/nuclear-experts-play-down-threat-uranium-stolen-isis-n152926.
22 Heather Saul, “Isis claims it could buy its first nuclear weapon from Pakistan within a year,” The Independent, May 23, 2015, https://www.independent.co.uk/news/world/middle-east/isis-claims-it-could-buy-its-first-nuclear-weapon-from-pakistan-within-12-months-10270525.html.
23 Matthew G. Bunn, “Securing the Bomb 2010: Securing All Nuclear Materials in Four Years,” Belfer Center for Science and International Affairs, (April, 2010), 1-14, http://nrs.harvard.edu/urn-3:HUL.InstRepos:29914176; Rens Lee, “Why Nuclear Smuggling Matters,” Orbis 52, no. 3 (2008): 434-44; and Peter D. Zimmerman and Jeffrey G. Lewis, “The Bomb in the Backyard,” Foreign Policy, no. 157 (2006): 32-39, accessed December 1, 2019 http://www.jstor.org/stable/25462103.
24 Christopher C. Joyner, “Countering Nuclear Terrorism: A Conventional Response,” European Journal of International Law 18, no. 2 (2007): 225-51.
25 Rolf Mowatt-Larssen, “Al Qaeda Weapons of Mass Destruction Threat: Hype or Reality?” Belfer Center for Science and International Affairs (January 2010) https://www.belfercenter.org/publication/al-qaeda-weapons-mass-destruction-threat-hype-or-reality.
26 Charles Daniel Ferguson and Michelle M. Smith, “Assessing Radiological Weapons: Attack Methods and Estimated Effects,” Defence Against Terrorism Review 2, no. 2 (Fall, 2009): 15-34.
27 Sammy Salama and Lydia Hansell, “Does Intent Equal Capability? Al-Qaeda and Weapons of Mass Destruction,” The Nonproliferation Review 12, no. 3 (2005): 615-53, https://www.aclu.org/sites/default/files/field_document/ACLURM002136.pdf.
28 James Forest, “Framework for Analyzing the Future Threat of WMD Terrorism,” Journal of Strategic Security 5, no. 4 (2012): 51-68.
29 Matthew Bunn and Anthony Wier, “Terrorist Nuclear Weapon Construction: How Difficult?” Annals of the American Academy of Political and Social Science 607, no. 1 (2006): 133-49.
30 FBI 100, “First Strike: Global Terror in America,” Federal Bureau of Investigation (February 26, 2008) https://archives.fbi.gov/archives/news/storie/2008/february/tradebom_022608 and Jonathan B. Tucker, Toxic Terror: Assessing Terrorist Use of Chemical and Biological Weapons, ed. Jonathan B. Tucker (Cambridge, MA: MIT Press, 2000): 320.
31 Mowatt-Larssen, “Al Qaeda Weapons of Mass Destruction.”
32 Daniel Koehler and Peter Popella, “Mapping Far-right Chemical, Biological, Radiological, and Nuclear (CBRN) Terrorism Efforts in the West: Characteristics of Plots and Perpetrators for Future Threat Assessment,” Terrorism and Political Violence (August 15, 2018) https://doi.org/10.1080/09546553.2018.1500365.
33 Camille Jackson, “Cyanide Bomb Found in Texas Owned by Racist, Anti-Semitic Couple William Krar and Judith Bruey,” Intelligence Report, April 20, 2004, https://www.splcenter.org/fighting-hate/intelligence-report/2004/cyanide-bomb-found-texas-owned-racist-anti-semitic-couple-william-krar-and-judith-bruey.
34 Deborah Tedford, “Scientist In Anthrax Case Dead Of Apparent Suicide,” NPR, August 01, 2008, https://www.npr.org/templates/story/story.php?storyId=93161970.
35 Audrey Kurth Cronin, “Terrorist Motivations for Chemical and Biological Weapons Use: Placing the Threat in Context,” CRS Report RL31831 (Washington D. C.: Congressional Research Services, the Library of Congress, 2003) https://fas.org/irp/crs/RL31831.pdf.
36 Paul D. Brister and Nina A. Kollars, “Pass Em’ Right: Assessing the Threat of WMD Terrorism from America's Christian Patriots,” Perspectives on Terrorism 5, no. 2 (2011): 50-66, http://www.terrorismanalysts.com/pt/index.php/pot/article/view/brister-pass-em-right.
37 Timothy A. Swanson, “Affidavit in Support of Criminal Complaint,” United States District Court Case no. 8:17 (May 20, 2017) https://www.justice.gov/usao-mdfl/press-release/file/968111/download.
38 Filippa Lentzos and Nikolas Rose, “Governing Insecurity: Contingency Planning, Protection, Resilience.” Economy and Society 38, no. 2 (2009): 230-54.
39 Richard Danzig, et al., Aum Shinrikyo: Insights Into How Terrorists Develop Biological and Chemical Weapons, 2nd ed. (Washington D.C.: Center for a New American Security, December, 2012), 52. https://www.cnas.org/publications/reports/aum-shinrikyo-second-edition-english.
40 Ibid. 36.
41 Richard Danzig, et al., Aum Shinrikyo. 27-38.
42 Michael K. Jacobs, “The History of Biologic Warfare and Bioterrorism,” Dermatologic Clinics 22, no. 3 (2004): 231-46.
43 Anna Pluta and Peter Zimmerman, “Nuclear Terrorism: A Disheartening Dissent.” Survival 48 no. 2 (2006): 55- 69.
44 Committee on Government Affairs, “Global Proliferation of Weapons of Mass Destruction,” (Washington D.C.: U.S. Government Printing Office, 1996): 30-31, ISBN 0-16-052543-8, https://archive.org/stream/globalproliferat01unit/globalproliferat01unit_djvu.txt.
45 Bruce Hoffman, “The First Non-state Use of a Chemical Weapon in Warfare: The Tamil Tigers Assault on East Kiran,” Small Wars & Insurgencies 20, no. 3-4 (2009): 463-77.
46 Alethia H. Cook, Terrorist Organizations and Weapons of Mass Destruction: U.S. Threats, Responses, and Policies, (Lanham: Rowman & Littlefield, 2017), 38-39.
47 Jacobs, “The History of Biologic Warfare and Bioterrorism.”
48 Ackerman and Jacome, “WMD Terrorism,” 24.
49 Jeffrey M. Bale and Gary A. Ackerman, “Profiling the WMD Terrorist Threat,” in WMD Terrorism: Science and Policy Choices, ed. Stephen M. Maurer (Cambridge: The MIT Press, 2009), 11-45.
50 Daniel Koehler and Peter Popella, “Beware of CBRN Terrorism - From the Far-Right,” Small Wars Journal, https://smallwarsjournal.com/jrnl/art/beware-of-cbrn-terrorism-from-the-far-right.
51 Saikh Nasir bin Hamid al-Fahd issued a fatwa entitled “A Treatise on the Legal Status of Using Weapons of Mass Destruction Against Infidels” March 2003 according to jihadi websites. Some quotes can be seen full text of “Islamic Books - Current Affairs and Islamic History (Part 17),” https://archive.org/stream/IslamicBooks-CurrentAffairsIslaamicHistoryPart17/ImperialHubris_djvu.txt.
52 Tim Lister and Paul Cruickshank, “From the grave, al-Awlaki calls for bio-chem attacks on the U.S.,” CNN Security Clearance, May 02, 2012, http://security.blogs.cnn.com/2012/05/02/from-the-grave-al-awlaki-calls-for-bio-chem-attacks-on-the-u-s/.
53 Henry Samuel, “Man charged after French police foil Paris ricin terror plot,” The Telegraph, May 18, 2018, https://www.telegraph.co.uk/news/2018/05/18/french-police-foil-ricin-terror-plot-arrest-egyptian-brothers.
54 Jörg Diehl and Fidelius Schmid, “Ermittler müssen gewaltige Datenmengen auswerten,” Spiegel Online, July 07, 2018, http://www.spiegel.de/netzwelt/netzpolitik/koeln-terrorverdaechtiger-islamist-hortete-daten-auf-handys-a-1217048.html.
55 Florian Flade, “The June 2018 Cologne Ricin Plot: A New Threshold in Jihadi Bio Terror,” CTC Sentinel 11, no.7, (August 2018):1-4, https://ctc.usma.edu/june-2018-cologne-ricin-plot-new-threshold-jihadi-bio-terror.
56 Tom Allard, “Exclusive: Indonesian militants planned ‘dirty bomb’ attack - sources,” Reuters, August 25, 2017, https://www.reuters.com/article/us-indonesia-security-idUSKCN1B51FW.
57 Europol, “European Union Terrorism Situation and Trend (TESAT) Report 2018,” 2018, 14, https://www.europol.europa.eu/activities-services/main-reports/eu-terrorism-situation-and-trend-report.
58 “Anders Behring Breivik’s Complete Manifesto ‘2083 – A European Declaration of Independence,’” Public Intelligence (July 28, 2011): 960-1027. https://publicintelligence.net/anders-behring-breiviks-complete-manifesto-2083-a-european-declaration-of-independence/.
59 “2018: A Year of Explosive Violence,” Action on Armed Violence (AOAV), January 10, 2019. https://aoav.org.uk/2019/2018-a-year-of-explosive-violence.
60 Ted Robert Gurr, “Which Minorities Might Use Weapons of Mass Destruction?” International Studies Review 7, no. 1 (2005): 143-46 and Sonia Ben Ouagrham-Gormley, “Barriers to Bioweapons: Intangible Obstacles to Proliferation,” International Security 36, no. 4 (2012): 80-114.
61 Ouagrham-Gormley, “Barriers to Bioweapons.”
62 Stephen Hummel, “The Islamic State and WMD: Assessing the Future Threat,” CTC Sentinel 9, no.1 (January 2016): 18-21, https://ctc.usma.edu/the-islamic-state-and-wmd-assessing-the-future-threat.
63 Cheryl Loeb, “Jihadists and Biological and Toxin Weapons,” in Jihadists and Weapons of Mass Destruction, eds. Gary Ackerman and Jeremy Tamsett (Boca Raton: CRC Press, 2009), 165.
64 Other hurdles could be the ability to accurately calculate the necessary infectious dose, achieve optimal composition formulation, prevent incremental degradation while transporting, and assess difficult to control environmental factors during delivery. See Ackerman and Jacome, “WMD Terrorism,” 28.
65 Charles D. Ferguson, “Radiological Weapons and Jihadist Terrorism,” in Jihadists and Weapons of Mass Destruction, eds. Gary Ackerman and Jeremy Tamsett (Boca Raton: CRC Press, 2009), 174.
66 Amy Frumin, Tracy Moss, and David Ellis, “The State of the Art in Contemporary CWMD Thinking,” PRISM 7, no. 3, (May 15, 2018): 68-83,https://cco.ndu.edu/News/Article/1507416/the-state-of-the-art-in-contemporary-cwmd-thinking.
67 Stephen Hummel, John Burpo, and James Bonner, “Profit-Minded Suppliers: Convergence of IED Facilitation and WMD Proliferation Networks for Non-State Actors,” CTC Sentinel 12, no.2 (February 2019): 12-16, https://ctc.usma.edu/profit-minded-suppliers-convergence-ied-facilitation-wmd-proliferation-networks-non-state-actors.
68 Ibid. This information can also be found in the “Global Improvised Threat Trends Update,” Joint Improvised Threat Defeat Organization, October 22, 2018.
69 John P. Caves, “Globalization and WMD Proliferation Networks: The Policy Landscape,” Strategic Insights 5, no. 6 (Naval Postgraduate School Center for Contemporary Conflict, July 2006), accessed December 2019, https://www.hsdl.org/?abstract&did=464919.
70 Hummel et al., “Profit-Minded Suppliers.”
71 Desmond Butler, The Associated Press, and Vadim Ghirda, “Nuclear smugglers sought extremist buyers, investigation uncovers,” Military Times, October 7, 2015, https://www.militarytimes.com/news/your-military/2015/10/07/nuclear-smugglers-sought-extremist-buyers-investigation-uncovers.
72 Ibid.
73 “State Security Service Detained Two Individuals on the Fact of Illegal Handling and Sale of Nuclear Material,” State Security Service of Georgia, March 13, 2019, https://ssg.gov.ge/en/news/450/saxelmtsifo-usafrtxoebis-samsaxurma-birtvuli-masalisadmi-ukanono-mopyrobisa-da-gasaghebis-faqtze-ori-piri-daakava.
74 Margarita Antidze, “Georgia detains six it says were trying to sell uranium,” Reuters, April 18, 2016, https://www.reuters.com/article/us-georgia-uranium-idUSKCN0XF1HM.
75 Brian Dodwell, Daniel Milton, and Don Rassler, “The Caliphate’s Global Workforce: An Inside Look at the Islamic State’s Foreign Fighter Paper Trail,” Combating Terrorism Center at West Point (April, 2016) https://ctc.usma.edu/the-caliphates-global-workforce-an-inside-look-at-the-islamic-states-foreign-fighter-paper-trail/ and Columb Strack, “The Evolution of the Islamic State’s Chemical Weapons Efforts,” CTC Sentinel 10, no. 9 (October 2017): 19-23 https://ctc.usma.edu/the-evolution-of-the-islamic-states-chemical-weapons-efforts.
76 H. A. Hasan, “IS Tests Chemical Weapons on Prisoners,” Basnews, May 23, 2016, http://www.basnews.com/index.php/en/news/iraq/277520.
77 Hamza Hendawi, Qassim Abdul-Zahra, and Ken Dilanian, “Officials: Islamic State seeking chemical weapons,” The Times of Israel, November 19, 2015, https://www.timesofisrael.com/officials-islamic-state-seeking-chemical-weapons and Kyle Orton, “The Islamic State and Chemical Weapons,” Kyle Orton’s Blog, September 30, 2016, https://kyleorton1991.wordpress.com/2016/09/30/the-islamic-state-and-chemical-weapons.
78 James R. Clapper, “Statement for the Record: Worldwide Threat Assessment of the US Intelligence Community,” U.S. Senate Armed Services Committee, February 9, 2016, 9, https://www.armed-services.senate.gov/imo/media/doc/Clapper_02-09-16.pdf and Emily Mullin, “Obama Advisers Urge Action against CRISPR Bioterror Threat,” MIT Technology Review. November 17, 2016, https://www.technologyreview.com/s/602934/obama-advisers-urge-action-against-crispr-bioterror-threat.
79 Incident and Trafficking Database, “2019 Fact Sheet: Incidents of nuclear and other radioactive material out of regulatory control,” International Atomic Energy Agency, https://www.iaea.org/sites/default/files/19/04/itdb-factsheet-2019.pdf.
80 Gary Ackerman and Michelle Jacome, “WMD Terrorism,” 26.
81 Harriet Alexander and Alastair Beach, “How Isil is funded, trained and operating in Iraq and Syria,” The Telegraph. August 23, 2014, https://www.telegraph.co.uk/news/worldnews/middleeast/iraq/11052919/How-Isil-is-funded-trained-and-operating-in-Iraq-and-Syria.html.
82 Paul Cruickshank, “A View from the CT Foxhole: An Interview with Hamish De Bretton-Gordon, Former Commander of U.K. CBRN Regiment,” CTC Sentinel 11, no. 7 (August 2017): 5-9, https://ctc.usma.edu/view-ct-foxhole-interview-hamish-de-bretton-gordon-former-commander-u-k-cbrn-regiment.
83 Europol, “European Union Terrorism Situation and Trend Report 2017,” 2017, 16, https://www.europol.europa.eu/tesat/2017.
84 Gabriela Martinez and Joshua Partlow, “Stolen cobalt-60 found in Mexico; thieves may be doomed,” The Washington Post, December 05, 2013, accessed December 2019, https://www.washingtonpost.com/world/stolen-cobalt-60-found-in-mexico-curious-thieves-likely-doomed/2013/12/05/262ef990-5d66-11e3-8d24-31c016b976b2_story.html?utm_term=.93c03d0b688d.
85 Europol, “European Union Terrorism Situation and Trend Report 2016,” 2017, 14, https://www.europol.europa.eu/activities-services/main-reports/european-union-terrorism-situation-and-trend-report-te-sat-2016.
86 Ibid.
87 “Breaking Bad fan jailed over Dark Web ricin plot,” BBC News, September 18, 2015, https://www.bbc.com/news/uk-england-34288380.
88 Europol, “European Union Terrorism Situation and Trend Report 2015,” 2015, 12, https://www.europol.europa.eu/activities-services/main-reports/european-union-terrorism-situation-and-trend-report-2015.
89 Columb Strack, “The Evolution of the Islamic State’s Chemical Weapons Efforts,” CTC Sentinel 10, no. 9 (October 2017): 19-23, https://ctc.usma.edu/the-evolution-of-the-islamic-states-chemical-weapons-efforts.
90 Jerrold M. Post, "Differentiating the Threat of Chemical and Biological Terrorism: Motivations and Constraints." Peace and Conflict: Journal of Peace Psychology 8, no. 3 (2002): 187-200.
About the Authors
Lasha Giorgidze is a Chemical, Biological, Radiological, Nuclear and Explosives (CBRNE) Specialized Officer who has worked for INTERPOL since 2013. Before joining INTERPOL, he served in law enforcement agencies in Georgia for almost ten years. Currently he is engaged in a number of programs directed at enhancing INTERPOL member countries capabilities in CBRNE prevention, preparedness, response and recovery. He has wide experience in the planning and delivery of international operations. Mr. Giorgidze has coordinated numerous multi-agency law enforcement operations targeting the illicit movement of CBRNE materials across international borders.
James K. Wither is a Professor of National Security Studies at the George C. Marshall European Center for Security Studies (GCMC) in Garmisch-Partenkirchen, Germany. He is a retired British Army Officer and former researcher in 20th Century Warfare at the Imperial War Museum, London. He has published widely on the subject of warfare, terrorism, and Western security and has lectured or taught at a variety of institutions, including the FBI Academy, the UK Defence Academy, the NATO School, the Geneva Centre for Security Policy, and the Afghan Army Staff College.
The George C. Marshall European Center for Security Studies
The George C. Marshall European Center for Security Studies is a leading transatlantic defense educational and security studies institution. It is bilaterally supported by the U.S. and German governments and dedicated to the creation of a more stable security environment by advancing democratic institutions and relationships, especially in the field of defense; promoting active, peaceful security cooperation; and enhancing enduring partnerships among the countries of North America, Europe, and Eurasia.
The Marshall Center Occasional Paper Series seeks to further the legacy of the Center’s namesake, General George C. Marshall, by disseminating scholarly essays that contribute to his ideal of ensuring that Europe and Eurasia are democratic, free, undivided, and at peace. Papers selected for this series are meant to identify, discuss, and influence current defense related security issues. The Marshall Center Occasional Paper Series focus is on comparative and interdisciplinary topics, including international security and democratic defense management, defense institution building, civil-military relations, strategy formulation, terrorism studies, defense planning, arms control, stability operations, peacekeeping, crisis management, regional and cooperative security. The Marshall Center Occasional Papers are written by Marshall Center faculty and staff, Marshall Center alumni, or by individual, invited contributors, and are disseminated online and in a paper version.
The views expressed in this publication are those of the author(s) and do not necessarily reflect the official policy or position of the George C. Marshall European Center for Security Studies, the U.S. Department of Defense, the German Ministry of Defense, or the U.S. and German Governments. This report is approved for public release; distribution is unlimited.
The George C. Marshall European Center for Security Studies in Garmisch-Partenkirchen, Germany, a German-American partnership, is committed to creating and enhancing worldwide networks to address global and regional security challenges. The Marshall Center offers fifteen resident programs designed to promote peaceful, whole of government approaches to address today’s most pressing security challenges. Since its creation in 1992, the Marshall Center’s alumni network has grown to include over 13,985 professionals from 157 countries. More information on the Marshall Center can be found online at www.marshallcenter.org.