
Jihadist Terrorist Use of Strategic Communication Management Techniques
Abstract
As long as the East bloc existed, military conflicts were largely determined by the policy of the USA and the USSR and were therefore part of the East-West conflict. Since this symmetrical- global conflict was decided in favor of the West, numerous asymmetrical conflicts have erupted around the globe in the aftermath. Terrorist conflicts have become a worldwide menace. Jihadist terrorism has spread beyond the borders of the regions in which it had its origin and has reached a global dimension. To offset this threat requires knowledge of what motivates, feeds and sanctions jihadist terrorists and their followers. Research and analysis of the root causes and underlying conditions, motivators and enablers of terrorism including the agitation propaganda of jihadist terrorists are vital to shaping appropriate countermeasures to the threat from Islamic terrorism. The interaction and dependencies between media and terrorism are still to be fully investigated. Research gaps exist concerning the media effects of terrorism and its interaction therewith. In particular, the utilization of the Internet by terrorists needs further research. One way to begin this investigation, the approach this paper takes, is to look at the jihadist use of strategic communication management techniques according to the elements that are used to generate a strategic communication management plan.
The theoretical jihadist terrorist communication plan described in this paper shows that the jihadist terrorist know how to apply strategic communication management techniques. The mass media and especially the Internet have become the key enablers and the main strategic communication assets for terrorists and have ensured them a favorable communication asymmetry. With these assets, terrorists are able to compensate for a significant part of their asymmetry in military might. Jihadist terrorists place a great deal of emphasis on developing comprehensive communication strategies in order to reach their desired short-, mid- and long- term goals and desired end states. Their ability to develop and implement such sophisticated strategies shows their fanatic conviction and their professionalism. Their communication goals are aimed at legitimizing, propagating and intimidating. They craft their strategies based on careful audience analysis and adapt their messages and delivery methods accordingly, adhering to the fundamental rules underlying any communication or public relations campaign. Their skillful use of the mass media and the Internet to compensate for asymmetrical disadvantages has enabled them to keep generating new generations of jihadist terrorists.
This information asymmetry must be undermined in order to counter the threat of a growing radicalization of the Muslim community. Ensuring ones own credibility while undermining the jihadists’ credibility is one of the key elements to winning this battle. It is possible to counteract the three primary terrorist communication goals, the propagation and enlargement of their movement, the legitimization of their movement and the coercion and intimidation of their enemies. Next to eliminating root causes and alleviating the underlying conditions, motivators and enablers of terrorism, such as terrorists' physical bases, developing an effective counter strategic communication plan, which exploits weaknesses and contradictions in the jihadists' use of strategic communication management techniques, is vital in winning the asymmetrical conflict with jihadist terrorists.
To successfully employ a strategic counter communication plan, it has to be embedded in a comprehensive approach of coercive military and law enforcement measures and conciliatory political, diplomatic and socioeconomic measures. These measures and the counter communication plan have to be synchronized at all levels of government (political, diplomatic, law enforcement, military, and intelligence) and with our partners and allies, to harmonize international efforts in the global war on terror within a grand strategy. This grand strategy, a comprehensive approach as security philosophy is an all-embracing approach that can only be developed in networked security structures based on a comprehensive international security rationale that effectively combines civilian and military instruments.
Next to developing a grand strategy to offset Jihadist Terrorists as a prerequisite, we need to focus more international research resources on countering the operational effectiveness of terrorist use of the mass media and the Internet, to undermine jihadist terrorist strategic communication operations. We need to address the root causes and hit the center of gravity, the tipping point of the Islamic society, by implanting messages and building the critical mass, cresting the threshold, when the key target audience-multipliers unleash a social epidemic in shifting views (Gladwell 2006) to turn the asymmetry in against the terrorists. Gaining a favorable communication asymmetry, is a major key to hitting the opponent at their center of gravity or several conflict-determining centers in order to win this asymmetrical conflict by eliminating its root cause(s) and communicating these facts. If the jihadist terrorists' effective strategic communication management techniques, in particular, their use of the Internet, can be curtailed by a counter communication plan embedded in a grand strategy and in an internationally unified effort, the basis of their favorable asymmetry can be eroded. If jihadist terrorists can be prevented from finding new physical bases in safe havens or in ungoverned areas including the ones in the World Wide Web, global jihadism may ultimately prove to be yet another fanatical backlash, which eventually fades.
1. Introduction
During the Cold War, military conflicts were largely determined by the policy of the USA and the USSR and were therefore part of the East-West conflict. Since this symmetrical-global conflict was decided in favor of the West, numerous asymmetrical conflicts have erupted around the globe in the aftermath. Terrorist actions, like the attack in Mumbai, India in November 2008, have become a worldwide menace. Jihadist terrorism1 has spread beyond the borders of the regions in which it had its origin and has reached a global dimension. The terrorist abuse of airliners as bombs on September 11, 2001 was a sad climax in this new dimension of asymmetrical of conflicts. To offset this threat requires knowledge of what motivates, feeds and sanctions jihadist terrorists and their followers. Research and analysis of the root causes and underlying conditions, motivators and enablers of terrorism including the agitation propaganda of jihadist terrorists are vital to shaping appropriate countermeasures to the threat from Islamic terrorism.
2. Key Terminology
There is no generally accepted academic definition of terrorism or asymmetrical conflict. A look at the history of war shows that the symmetrical war, a war between equal opponents, is the exception, whereas asymmetrical wars and conflicts seem to be the norm. One could argue that in wars, the conflict is always about the creation of unequal, asymmetrical relations in favor of one’s own side in order to win the campaign. If one speaks about the art of war, one has to consider the following battle space dimensions: knowledge, strength, time and space, all in conjunction with ingenuity.Knowledge stands for high-quality, mission-relevant information that is readily available to one’s own side but is kept from the opponents, in order to guarantee qualitative knowledge superiority. Strength stands for quantity and quality of force in every dimension. Time refers to speed, endurance, timeliness, diligence, or a combination thereof. Space describes area, depth, sphere and society. Ingenuity conveys the astuteness of the leadership qualities, the use of unconventional actions and/or the refusal to follow conventions. The art behind great military leadership is the art of creating and applying asymmetry in all five dimensions. As Carl von Clausewitz put it: “[...] the seeds of wisdom that are to bear fruit in the intellect are sown less by critical studies and learned monographs than by insights, broad impressions, and flashes of intuition” (Carl von Clausewitz).
In conflicts and wars between states, one speaks of symmetrical conflicts, in spite of existing or aimed-for asymmetries. But inter-state conflicts are not considered to be asymmetrical conflicts, since they have a substantially smaller asymmetric dimension (König 2004).
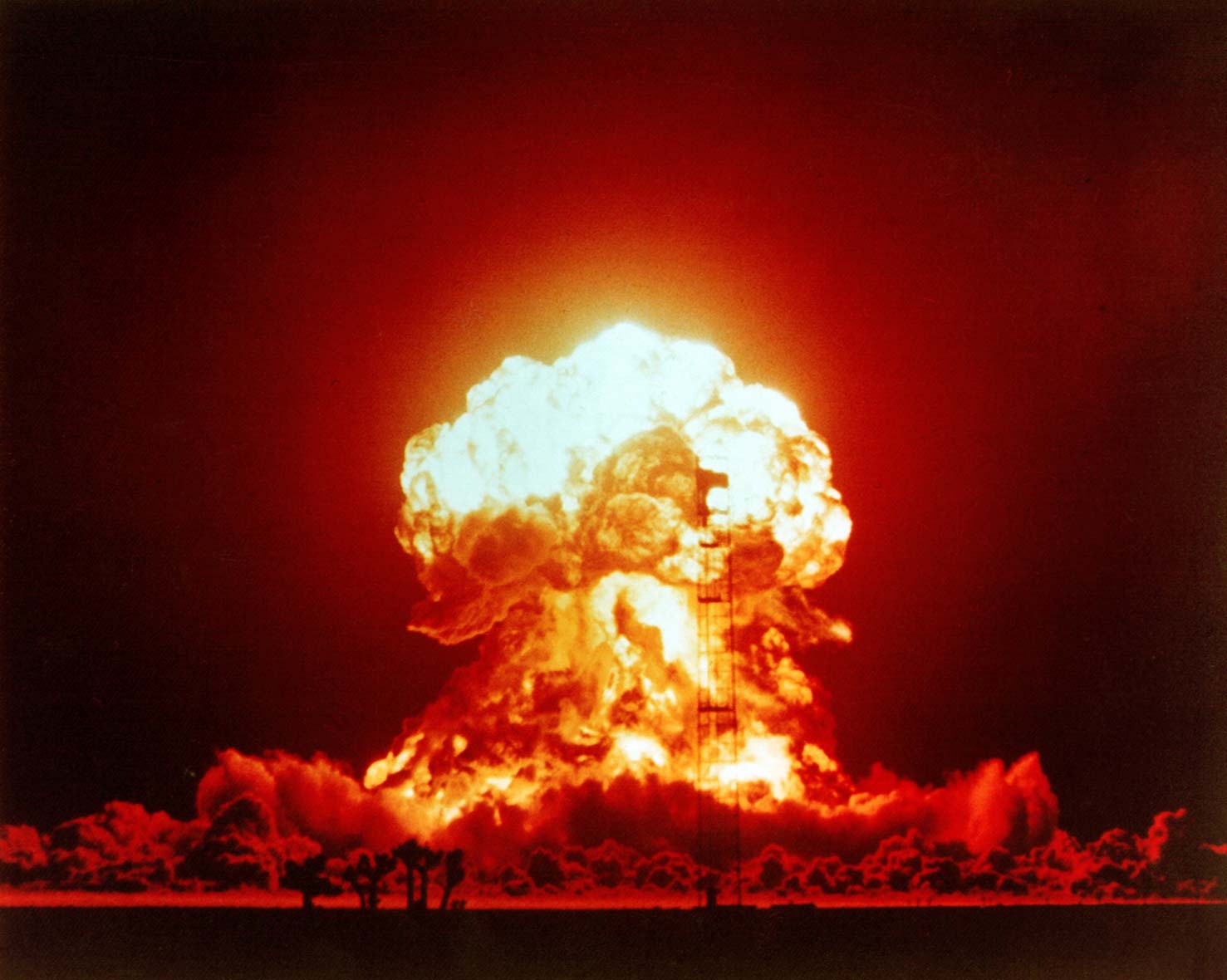
2.1 Asymmetrical Conflicts
These are conflicts between parties that show essential quantitative and/or qualitative dissimilarities in the battle space dimensions: an imbalance in forces, a different determination/ motivation, a different legitimization, a different application of methods and a difference in the quality or character of methods themselves. Asymmetrical conflicts are usually waged in a changing, asynchronous and unpredictable manner. The purpose is to hit the opponent at his center of gravity or several conflict-determining centers and decide the conflict in one’s own favor or to reach one’s own purposes. A new dimension of asymmetrical conflicts stems from the use of the mass media, especially the Word Wide Web, to spread information, the worldwide consequences of such conflicts and the increased threat of the use of weapons of mass destruction by terrorists (Münkler 2006, Geyer 2004).
2.2 Terrorism
The discipline of terrorism research is relatively young and has likewise no generally accepted academic definition for terrorism. The word terror comes from the Latin word terrere, which means to frighten or scare. The concept of terrorism goes back to the 19th century. Terrorism as a political-military strategy has existed for about 40 years. The recent combination with the global mass media has allowed terrorism to reach a global dimension. In this paper, terrorism is defined as political violencein an asymmetrical conflict that is designed to induce terror and psychic fear (sometimes indiscriminate) through the violent victimization and destruction of noncombatant targets (sometimes iconic symbols). Such acts are meant to send a message from an illicit clandestine organization. The purpose of terrorism is to exploit the media in order to achieve maximum attainable publicity as an amplifying force multiplier in order to influence the targeted audience(s) in order to reach short- and midterm political goals and/or desired long-term end states.
Terrorists do not primarily aim at the physical, but on the psychological effect of their attacks. Terrorism uses a strategy that primarily relies on the symbolic strength of the act. The use of terror serves not primarily the purposes of fighting, injuring or destroying the opponent. Rather, its primary purpose lies in the conveying of messages to the target audience(s). Terrorists perpetrate their acts without regard for war fighting conventions. The symbolism originating from terrorist acts and media marketing thereof is intended to address the public, to use them as a vehicle and a communication channel to influence the political representatives/decision makers and other target audiences. Terrorists fight with limited resources from the underground against an adversary unbeatable by military means. Terrorist groups often proclaim themselves to be guerrillas or to have to lead a partisan’s fight with unconventional fighting methods to compensate for their military inferiority. Unlike some kinds of partisans, terrorists are not capable to win a direct military confrontation and therefore avoid it (Bockstette 2006). Terrorists are generally driven to commit acts of terrorism to express and redress their grievances and demands due to a variety of factors, which can be rational or irrational. These root causes usually consist of multiple static or dynamic combinations of factors and circumstances, ranging from general to specific conditions, motivators and enablers. They can be global, regional or local, societal, structural or psychological. Some of these causes may be more important than others (Sinai 2008).
2.3 Strategic Communication Management
For the purposes of this paper, strategic communication management is defined as the systematic planning and realization of information flow, communication, media development and image care in a long-term horizon. It conveys deliberate message(s) through the most suitable media to the designated audience(s) at the appropriate time to contribute to and achieve the desired long-term effect. Communication management is process creation. It has to bring three factors into balance: the message(s), the media channel(s) and the audience(s) (Bockstette, Quandt & Jertz 2006).
The interaction and dependencies between media and terrorism are still to be fully investigated. Research gaps exist concerning the media effects of terrorism and its interaction therewith. In particular, the utilization of the Internet by terrorists needs further research. One way to begin this investigation, the approach this paper takes, is to look at the jihadist use of strategic communication management techniques according to the elements that are used to generate a strategic communication management plan:
3. Jihad Desired End State
Jihad terrorism is ostensibly motivated by an extreme interpretation of Islam. The use of violence is regarded by its practitioners as a divine duty or sacramental act (EUROPOL 2007). The Jihad terrorists’ self-proclaimed goal is to reinvigorate the Islamic Ummah2 and to mobilize the Muslim community in a revolutionary transformation of the Muslim world population in confrontation with the international order spearheaded by Western society. They strive toward the creation of a new world wide Islamic caliphate, which jihad terrorists widely consider the ideal Islamic form of government representing the political unity and leadership of the Muslim world. These goals and underlying root causes are the factors and circumstances that drive the jihad terrorists. In a 2006 interview, Abu Musab-al Zarqawi explained the jihadists’ goal thus:
“Our political agenda, [...] is that of the saying of the Prophet (peace be upon him), I have been sent with the sword, between the hands of the hour, until Allah is worshiped alone ... this is what determines our political goal. We fight in the way of Allah, until the law of Allah is implemented, and the first step is to expel the enemy, then establish the Islamic state, then we set forth to conquer the lands of Muslims to return them back to us, then after that, we fight the kuffar (disbelievers) until they accept one of the three. I have been sent with the sword, between the hands of the hour; this is our political agenda” (Jihad Unspun 2007).
3.1 Short-term Goals
In the short term, the jihadist terrorists aim for an enlargement of their supportive patronage. Therefore, the persuasion of the receptive Muslim audience via the heightening of an Islamic identity in confrontation with the West is one of their goals. This includes the wakening of the Muslim population by luring the U.S. into conflicts on the Arabian Peninsula in order to be able to engage the enemy directly. The terrorists need Western troops and their military action in the Muslim world to implement their media strategy. The presence of troops and their actions produce the desired graphic footage of western “occupation of the Islamic nations” that furthers their media-centered strategy. It thrives on images and words about every innocent civilian killed by Western bombs transmitted via television and Internet, producing intense antipathy towards the West. Building on this, the terrorists can more effectively call for the end of foreign influence in Muslim countries. Therefore, even though it is an obvious contradiction, another short-term goal is to drive those they call invaders from the Arabian Peninsula (Gendron 2007), even though the number of U.S. troops in Saudi Arabia was reduced in 2005. The most promising approach to this is to attack US coalition allies which are judged the most vulnerable (those with weak governments or poor public support for involvement), in order to induce their governments to pull out their troops. The underlying strategy is to isolate the US by splitting up and undermining its coalition, thereby indirectly forcing the US and its coalition to pull out. Therefore, the terrorists carry out a combination of attacks against US forces and US coalition forces. The Norwegian Defense Research Establishment provides evidence of this, quoting from the Media Committee for the Victory of the Iraqi People, a lengthy al-Qaeda planning document on a radical Islamic Web site in December 2003:
“We think that the Spanish government could not tolerate more than two, maximum three blows, after which it will have to withdraw as a result of popular pressure. If its troops still remain in Iraq after those blows, then the victory of the Socialist Party is almost secured, and the withdrawal of the Spanish forces will be on its electoral program” (Norwegian Defense Research Establishment 2004).
3.2 Intermediate Goals
In the mid-term, goals include the removal of all political leaders who currently govern secular Muslim states and the elimination of the state of Israel. The terrorists' aim is to install supportive Islamic regimes and transform from a decentralized network organization to a massive Islamic movement that strives toward their desired end state. Also, by conducting major attacks behind enemy lines, i.e., in Western nations, they put on a pageant show of force, which drives in the majority of the donations to the network (Musharbash 2006).
3.3 Long-term Goals
The jihadists’ primary long-term goal is to restore a devout Islamic caliphate by politically uniting all countries with a Muslim majority in an Islamic realm through a monolithic Islamic religious/ social movement. The desired end state is the caliphate’s rule worldwide (al-Zawahiri 2005).
4. Jihad Communication Goals
4.1 First Communication Goal
The jihadists’ communication strategy is inseparable from their political strategy, as their terrorism and rhetoric alike work toward the common goals and desired end state. Consequently, their communication goals are based on their short-, mid-, and long-term goals and the desired end state.
Their primary long-term strategic communication goal is the propagation and enlargement of their movement through the global spreading of information among the desired receptive Muslim audience. The terrorist communication strategy aims ultimately at a fundamental restructuring of the political discourse and identity of the Islamic world.
4.2 Second Communication Goal
The legitimization of their movement—establishing its social and religious viability while they engage in violent acts—requires a continuous communication effort. Their violent methods and killing of innocent people inevitably contradicts Islam. This built-in drag on the organization’s legitimacy (Gendron 2007) can in the long run only be circumvented through an unceasing communication effort in which, as Weimann notes, “Violence is presented as a necessity foisted upon the weak as the only means with which to respond to an oppressive enemy” (2004).
Therefore, legitimacy and the ostensible demonstration of compliance with Islamic law are prominent in their communication strategy. The utopia of their aimed-for end state and their Islamic-jihadist worldview fulfills a significant purpose: The utopia is not only the purpose, but also moral and religious justification. They try to portray their movement as one of freedom fighters, forced against their will to use violence due to a ruthless enemy that is crushing the rights and dignity of their community. This makes legitimization of their terrorist deeds their second strategic communication goal.
4.3 Third Communication Goal
The coercion and intimidation of the near enemy and far enemy is the third strategic communication goal. The near enemy is composed of apostates, or secular Muslim regimes, especially ones with Western support. The far enemy is, in their view, comprised of Jews, unbelievers, and Western society as a whole. They try to manipulate the near enemy in order to reach their mid-term political goal of removing the near enemy from power. They also try to intimidate the far enemy into a complete withdrawal from the Arabian Peninsula and refraining from supporting secular Muslim regimes, i.e. the near enemy. The desired end state, worldwide rule of a devout Islamic caliphate, is the all-embracing long-term communication goal.
5. Communication Infrastructure
5.1 Traditional Communicative Means
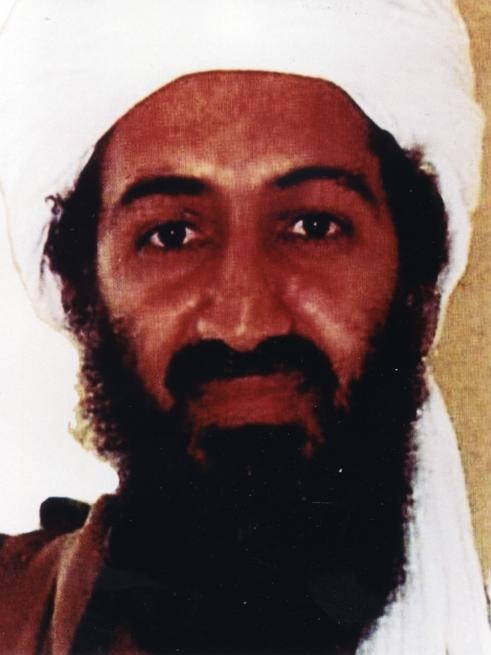
During the 1990s, terrorists communicated with their audience(s) by more traditional means, such as journalist interviews, fax, face-to-face propaganda and even press conferences. At the end of 1998, there was a shift in the primary strategic communications means due to technological advances and the rise of Al-Jazeera (Wojcieszak 2007). The Al-Jazeera television network became achannel for broadcasting their messages and Al-Jazeera would in turn provide the tapes to CNN and other international news corporations (Gendron 2007). To a certain extent, the media mutated from its role as a critical observer and reporter to a more and more active role as a conflict participant (Golan 2006). Gendron quotes an al-Qaeda spokesman in describing this shift:
“[...] Sheikh Usama knows that the media war is not less important than the military war against America. That’s why al-Qaeda has many media wars. The Sheikh has made al-Qaeda’s media strategy something that all TV stations look for. There are certain criteria for the stations to be able to air our videos, foremost of which is that it has not taken a previous stand against the mujahedeen. That maybe explains why we prefer Al-Jazeera to the rest” (Gendron 2007).
The jihadist terrorists carefully tapped into the “Al-Jazeera narrative”, sounding strictly those themes most likely to appeal. The main themes are the call for jihad against Israel, the end of the occupation of Palestine, the Arabian Peninsula and Afghanistan, and the end of the U.S. presence in the Persian Gulf region. Since the last Iraq war, themes have also included a call against the U.S. occupation of Iraq and against the corruption in existing Islamic regimes, including Pakistan.

5.2 New Media
After September 11, 2001, jihadist terrorists expanded their communication infrastructure and methods of communication considerably. That year saw the formation of the Al-Sahab (The Cloud) Islamic Media Publication Company. It is essentially the main entity of the media production division of al-Qaeda,which relies heavily on the Internet. It produces video files of interviews, documentaries, speeches or news programs. All known speeches by senior leadership of the original al-Qaeda released after June 2006 carry the al-Sahab logo. The frequency, quality and style of the video messages are getting more and more professional and the techniques used are increasingly sophisticated. The media rhetoric is mainly built around the visual component. Email, Skype and other VOIP programs are increasingly using visual modes of communication and the jihadist terrorists utilize this technology in conjunction with the Internet abundantly (Cardoso 2008). English, either spoken or in subtitles, is regularly the language of choice(Europol 2007). Other subgroups use different modus operandi and video production features like subtitles and logos. By creating their own training and operational video tapes, the terrorists groups support organizational learning in several ways, providing the groups producing the video with firsthand experience (learning by doing) and the audience viewing the video with secondhand experience (learning by imitation) (Salem & Reid & Chen 2008).
The new media provide the vehicle for the spreading of the terrorist message. The greater the violent audacity and the larger the scale of the cold-blooded brutality of the terrorist act, the more coverage it usually receives in the new media. Thereby the terrorists reach the global public, including any desired audience. They recognized the revolutionary significance of the evolution of the media infrastructure, perceptive of the fact that using strategic communication management can be on equal footing with conventional armed forces. In the media, international terrorism has at its disposal an instrument of substantial power with which it can compensate for a significant part of its asymmetry in military might. Terrorists have adapted innovative 21st century information and communications technologies and the associated infrastructure to maximize the psychological impact of their operations and communiqués through the use of video messages (Storsul & Fagerjord 2008).
The jihadist terrorist strategy is inextricably rooted in extensive use of the new media. This is underlined by the jihadists’ organizational structure in the mid-1990s through late 2001, which incorporated communication and media functions. The formal structure included a political, military and an information committee. The political committee was responsible for the wider political relations and the wider jihad movement. The military committee conducted the operations. The information committee provided the “(m)eans of communications setup in all categories of Islamic people, taking great pains in making it aware of its enemies’ plans, aspiring to concentrate all of the scientific, legal, and jihad capabilities in the first level in order to obstruct on line in front of the alliance of the infidel and the ugly ones” (Corman & Schiefelbein 2008).
5.3 Global Mass Media & the Internet
This organizational structure changed after the loss of Afghanistan as a physical base. The conversion from a clandestine organization to a decentralized, open network organization was the only possible means of survival. The dependence on the traditional mass media was compensated for and even excelled by the use of the Internet. The aim is to effect the transformation of dispersed followers and sympathizers in the Muslim community into self-made terrorists. The volunteer legwork by terrorist sympathizers is therefore highly welcomed.
After losing the base in Afghanistan, the size of the attacks was decreased to a victimization of around 50 to 200 casualties, like the Islamabad Marriott Bombing on September 20, 2008. The blast of 600 kg of RDX and TNT occurred hours after Pakistan’s new president, Asif Ali Zardari, told parliament the country would continue its fight against terrorism. The terrorist act occurred a few hundred yards form the prime minister’s house, where high-level government officials were dining after the address by the president to parliament. This dinner was moved form the Marriott Hotel at the last moment (OSAC 2008). The same rough victimization rate holds true for the attacks in Mumbai by Lashkar-e-Taiba,3 the terrorist group presumably responsible for the deadly attacks. The November 2008 Mumbai attacks were a series of eight coordinated attacks across Mumbai, India’s financial capital and its largest city, killing at least 101 people. The attacks began on November 26, 2008 and ended on November 29, 2008 when Indian security forces regained control of the attack sites.The complexity of the operation, the coordinated beach landing, GPS and Google usage showed that the level of sophistication of terrorist attacks is continuously increasing (BBC2008). Still, bigger and more complex operations with thousands of victims, like the one in New York 2001, are no longer the operational norm. The risk that big operations could be confounded is too great.

Jihadist terrorists now resort to the tactic of “guide-less resistance”, in which responsibility rests solely with the decentralized operator. Abu Musab al Suri wrote a lengthy essay on this scheme (Stern 2003). Al-Qaida concentrates on producing abstract directives and motivational calls in order to steer their movement. Processes running in parallel and coordination via the World Wide Web enable the jihadist terrorists to survive as a loosely connected network.
The emergent digital technologies expanded their communicative possibilities. By using the global mass media and the Internet as their main communication infrastructure, al-Qaida survives as a jihadist terrorist organization, through publishing written statements, blogs (Keller 2008), articles by ideological leaders and online-magazines (Europol 2007). The jihadist terrorists profit from the fact that the world of mass communication is evolving into a world of networked mediated mass communication, where different mediated technologies combine interpersonal mediation devices with mass communication ones. Those different media are connected through inter-personal media such as mobile phones, iPods, WiFi, etc. and the World Wide Web. The fusion of interpersonal communication and mass communication, connecting audiences—that all can also be publishers or broadcasters at the same time via the World Wide Web—enhances the resonating cavity of terrorists and greatly increases their access to audiences (Cardoso 2008).
Additionally, almost every major news organization offers site visitors the opportunity to upload content that, if compelling enough, will be featured online as user-generated content. Even newspapers regularly cite reader comments and depend on blog members as sources of cutting-edge social and political news. This user-generated content is now a fundamental component of the global communication network (Arsenault & Castells 2008). However, this use of the Internet also poses a dilemma. It is a major challenge to control a decentralized, amorphous and secretive organization, orienting it to a common objective via the Internet, while also maintaining organizational security (Corman & Schiefelbein 2008).
Dictatorships and totalitarian systems also pose challenges to terrorists trying to disseminate their messages. In dictatorships, the life of a person has far less value. The spread of information about a terrorist act via the media can be suppressed in dictatorships by government means, so that the terrorists lack a determining weapon: the mass media. Hence, terrorist acts are more effective in democracies. Democracies offer the ideal basic conditions for terrorism. Obviously, the principles of a democracy and the associated social structures are for terrorists the functional equivalent to what marshes and inaccessible mountain regions are for partisans. In particular, the media and the Internet enable terrorists to thrive in a cancerous manner in the freedom that democracies provide (Leptien 2002). Even though mainstream press tends to adhere mainly to official news sources, the terrorist message still receives abundant coverage. There is always the imminent danger that the mainstream press becomes the outlet for the state’s or the terrorists’ “spin” if their research and investigation does not provide the necessary intellectual context and depth (Lancaster 2008).
The intensive, sometimes obsessive coverage in the media about a terrorist act generates the desired psychological effect (Katz & Liebes 2007). Terrorist actions are planned and organized in a manner that causes a strategically maximum communicative effect, while requiring minimal resources.
Hence, based on a strategic communication plan and precise planning and consideration of the transmitting time, strategic considerations take place well in advance of a terrorist attack.
The increasing globalization of the media and satellite reporting as well as the rapid development of the Internet have extended the resonating cavity for terrorism and show the determining innovation of the terrorist use of force. The symbiotic relationship between terror events and the media is apparent: the perpetrators would have far less impact without media publicity and the media can hardly be expected to resist reporting (Katz & Liebes 2007). The marathon treatment of terror events may deprive the journalist of the time and distance the journalist needs to research, investigate and edit. An economic approach and an institutionalized perspective can help in understanding media events. They can be analyzed as products and outcomes of economic strategies whose aim is the accumulation of economic or symbolic capital, or the transformation of one type into the other (Krämer 2008).
The fusion of the Internet and satellite television (IP TV) will lead to a convergence of the different media, thereby strengthening this effect even further. This offers terrorists expanded possibilities of influencing and manipulating audiences. Already, terrorists make abundant use of the Internet for internal and external communication. They raise capital, franchise their brand name, recruit followers (Thomas 2005), find partners and suppliers, provide training materials through their online library and manage operations (Gendron 2007). Terrorists capture information about the users who browse their sites. Users who seem most interested in their terrorist cause or well suited to carrying out its work are then contacted.
Thanks to the communicative possibilities of the Internet, jihadist terrorist groups have become more numerous, agile, and well coordinated. Decades ago, before terrorism became an international phenomenon, local and regional media played a subordinated role. They were of limited use to jihadists, due to the governments’ ability to control their appearance:
“This was done by legislation, by putting pressure on the national media [...] over limiting exposure to terrorists. [...] The situation in which both terror and media were operating within the nation’s boundaries made it possible for governments to limit the terrorists’ capacity to exploit the media for creating public anxiety, enhancing their bargaining power while holding hostages, or communicating with their own supporters” (Stuart & Zelizer 2004: 79).
This changed dramatically with the increasing interlinking of terrorism and the technological advancement of the media and its communication infrastructure. The media’s worldwide “live reporting” via satellite TV has created the stage for a global media presence for the jihadist terrorists:
“The automatic, universal adoption of the genre of breaking new—that is, live marathonic broadcasting during, and in the wake of, a multi-victim attack—facilitates the upgrading of terrorists to superstars” (Stuart & Zelizer 2004: 81).
5.4 Islamic Media Structure
For years, terrorists could rely on an almost streamlined Islamic media infrastructure, which willingly conveyed the desired messages and videotapes and helped to shape a brand name. Until the advent of the Internet, terrorists focused their attention on television, radio or the print media. But these traditional media have “selection thresholds”, which are multistage processes of editorial selection over which terrorists have no control (Weimann 2004). In addition to this obstacle, by early 2003 the Arab media environment had begun to fragment, becoming increasingly crowded and competitive. A growing array of satellite television stations began to ensure competition and therefore a diversity of opinion, which hampers the communication strategy of the terrorists on the TV front. Arab television stations and their voices seem to be more capable of swaying the Islamic population away from jihadism than do the public diplomacy efforts of the Western nations. The quantity and volume of anti-jihad voices in the Arab media have dramatically increased since 2003, with every al-Qaeda-linked terror attack now being met by a chorus of Arab criticism and condemnation. Public opinion polls have shown steep declines in support for al-Qaeda, particularly in countries directly affected by its terror attacks. Arab satellite television became one of the strongest forces today pushing for change in the region and one of the biggest obstacles to al-Qaeda’s agenda of imposing a monolithic Islamic identity through a streamlined Islamic media voice. It therefore poses the greatest challenge for the terrorists’ political vision and accelerated the use of the Internet as an information-spreading platform to compensate for the loss of the now opposing satellite TV. This makes the Internet even more the key enabler and main strategic communication infrastructure asset for terrorists (Corman & Schiefelbein 2006). As Abu Omar expressed it, “We are the energy behind the path to jihad. Just like the jihadis reached their target on September 11, we will reach ours through the Internet” (Fattah 2006).
2003 also saw the publication of “Sawt al-Dschihad”, the first terrorist magazine published on the Internet. Even though its last issue appeared in April 2005, it found many imitators. Following its example, numerous terrorist groups in Iraq and North Africa began publishing magazines, which provoked a warning not to abuse brand names. In 2004, Saudi al-Qaeda said that “Voice of the Jihad” is the property of Saudi al-Qaeda and called on imitators to develop and franchise their own brand names (Musharbash 2006).
In the jihad terrorism web infrastructure (Chen et al. 2008), websites suddenly emerge, frequently modify their formats, swiftly disappear, or change their online address (Weimann 2004). More recently, the use of static websites has declined in light of the fact that these websites are still relatively easily closed down by hackers or law enforcement agencies. Now terrorists utilize online forums and blogs as a more secure way of disseminating their propaganda material. These forums offer access to files stored on free storage sites. Since this material is spread over numerous web servers located all round the globe, blocking access to these files becomes virtually impossible (Europol 2007).
6. Target Audience(s) and Communication Channels
While some propaganda messages are intended for a broad audience, the majority are tailored to a particular target group. The messages, the channels by which these messages are communicated, and the languages they use are tailored to the special needs of the target group. The terrorists select and segment the strategically desired target audience, the transmitting medium, and the targets for destruction. They determine the location and timing of their actions to satisfy media criteria for news worthiness that fit in with the media’s deadlines and news cycles in order to effectively reach the desired audience. The actual violent operation is embedded within their strategic communication efforts. Herein the Internet is becoming more and more important as a communication channel. It offers easy access, little or no regulation and censorship, potentially huge audiences, anonymity, and fast flow of information, all at relatively little expense (Weimann 2004).
Jihadist Terrorists exploit the unique attributes of the Internet. It offers the possibility to communicate in near real time. The Internet is also used extensively as a terrorist knowledge transfer base and education medium for their own followers. Further, they use the medium extensively for command and control to gather intelligence and to distribute information among their sympathetic audience. The Internet has enabled the rise of numerous loose and decentralized terrorist networks and enables terrorist groups to operate like decentralized franchises or freelancers. The net enables the terrorists to operate as virtual transnational organizations and reach their audience(s) around the globe to maintain group identity, indoctrination and demonstrable implementation of its revolutionary ideology and principles (Gendron 2007). The Internet, as an uncensored medium, carries information regardless of its validity or potential impact. It allows even small groups to amplify their message and exaggerate their importance and the threat they pose (Weimann 2004).
Jihadist Terrorist groups use the Internet as mass media to exploit the abundant possibilities to sow disinformation, undermining diplomatic and military efforts and improving their own operational effectiveness. Consequently, some of their followers specialize in information warfare and regularly claim responsibility for attacks that have occurred or will take place. The grand masters in this discipline are the Abu Hafs al Masri brigades. Every time these dubious brigades claimed responsibility for an attack, the news agencies and security services jumped, although till this day not one brigade member has been caught who had a connection to the execution of the attack. They even claimed to be responsible for the power outages in August 2003 in parts of the United States (Carmon 2004).
The target audiences of the jihadist terrorists can be divided into the following addressees:
6.1.1 The Ummah Outsiders
Ummah is an Arabic word used to describe the Diaspora or “Community of the Believers” and thus the world community of Muslims. This group can be segmented into insiders and outsiders of the jihadi audience (Corman & Schiefelbein 2006; Gendron 2007). The outsiders include the sympathizers and the neutrals. They consist of the Muslims who could potentially be persuaded to become an ummah insider. In the long run, major portions of this audience are needed to realize the desired end state, a worldwide devout Islamic caliphate (Corman & Schiefelbein 2006). This means in consequence that the terrorists’ primary target audience is neither a minority of radicalized jihadists nor the public of the Western nations, but the vast majority of the Muslim public. Main communication channels consist of face-to-face methods utilizing prayers, speeches and sermons in mosques and Koran schools; the mass media; and increasingly, the Internet.
6.1.2 The Ummah Insiders
The insiders consist of the supporters and followers. They are committed Muslim radicals who provide operational, financial, or administrative support to the global jihadist terrorist movement (Corman & Schiefelbein 2006; Gendron 2007). For this audience, the main communication channel is the Internet and secondly the mass media.
Ayman al-Zawahiri, July 2005: “We are in a battle, and more than half of this battle is taking place in the battlefield of the media [...]. (W)e are in a media battle for the hearts and minds of our Ummah” (Whitlock 2006).
6.2 The Adversary Outsiders
This audience includes apostate secular Muslim regimes, sometimes referred to as troublemakers, and all unbelievers, the so-called crusaders, Zionists, apostates, Jews and the West, of which the United States is considered the leader (Gendron 2007). They are further dissected into the near enemy (apostates, secular Muslim regimes) and the far enemy (Jews, unbelievers, and Western society) (Whitlock 2006). The preferred communication channel for this group is the global mass media and secondly the Internet.
7. Findings and Recommendations
A written jihadist strategic communication management plan has not yet been intercepted. But that the jihadist terrorist use strategic communication management techniques is, as this article has shown, certain. They defined communication objectives, developed communication tactics and established needed strategies and many jihadist documents demonstrate that the jihadists do analyze their communication and media operations in order to enhance its overall effect on mission. The fact that the self proclaimed jihadist terrorists evaluate the effectiveness of their communications campaigns and even elaborate theoretically about how efficient their operations are (Corman & Trethewey & Goodall 2008), underlines their professionalism and the severity of their conviction. Systematically practicing after action reviews, they usually record the event on scene and monitor the media coverage and the spreading via the Internet thereafter.
The mass media and especially the Internet have become the key enablers and the main strategic communication assets for terrorists and have ensured them a favorable communication asymmetry.With these assets, terrorists are able to compensate for a significant part of their asymmetry in military might. Jihadist terrorists place a great deal of emphasis on developing comprehensive communication strategies in order to reach their desired short-, mid- and long-term goals and desired end states. Their ability to develop and implement such sophisticated strategies shows their fanatic conviction and their professionalism. Their communication goals are aimed at legitimizing, propagating and intimidating. They craft their strategies based on careful audience analysis and adapt their messages and delivery methods accordingly, adhering to the fundamental rules underlying any communication or public relations campaign. Their skillful use of the mass media and the Internet to compensate for symmetrical disadvantages has enabled them to keep generating new generations of jihadist terrorists.
This information asymmetry must be undermined in order to counter the threat of a growing radicalization of the Muslim community. Ensuring one’s own credibility while undermining the jihadists’ credibility is one of the key elements to winning this battle. It is possible to counteract the three primary terrorist communication goals, the propagation and enlargement of their movement, the legitimization of their movement and the coercion and intimidation of their adversaries. Next to eliminating root causes and alleviating the underlying conditions, motivators and enablers of terrorism, such as terrorists’ physical bases, developing an effective counter strategic communication plan, which exploits weaknesses and contradictions in the jihadists’ use of strategic communication management techniques, is vital in winning the asymmetrical conflict with jihadist terrorists.
This plan has to be embedded into a greater strategic plan. This plan, as a grand strategy and comprehensive unified approach, needs to counter terrorism by achieving a favorable asymmetry in all five dimensions of modern warfare: knowledge, strength, time, space, and ingenuity at three levels: First, at the tactical level an operative coercive mechanism for deterrence (denial of opportunity) is needed to de-link the terrorist action from its intended victims. Second at the operational level, a mechanism of denial of capability, to disrupt the terrorist organizational recruitment, training, access to weapons and sanctuary, communications, finance and other resources is needed. Third, a mechanism at the strategic level, the denial of objectives – the marginalization of terrorist messages is a major necessity (Smith & Talbot 2008). Developing a counter strategic communication plan is a vital part thereof.
7.1 Intensify the Research on Root Causes
The first phase in developing an effective counter communication plan is research. The goal of this phase is to take a comprehensive look at all the variables that will have an impact on the development of a counter strategic communication plan. To attain a complete picture of the root causes that are driving the terrorists, it is crucial to research and synthesize the causes at different levels. This includes mapping the spectrum at the individual, group, societal and governmental levels. Addressing the underlying root causes that facilitate recruitment and support for jihadist terrorists, such as prevalence of regimes that stifle opportunities for educated youth to attain socioeconomic and political advancement, is an elementary part thereof (Sinai 2008). The research must also look at a range of coercive and conciliatory measures that address the general and specific root causes that give the rise to the jihadist terrorist networks. The root causes of terrorism are generally not static but rather dynamic and are a fundamental part of the center of gravity. In the long run al-Qaeda’s radical revisionism cannot succeed, unless its terrorist strategic communication management can win substantial support from the global Muslim community. But winning such support is unlikely. The 14th century ideology promoted by the jihadist terrorists and the indifferent killing of innocent Muslims holds little appeal for the majority of Muslims. They have no wish to live under a repressive theocratic dictatorship in a new Islamic caliphate striving for global domination. Furthermore, Arab satellite television has become one of the obstacles to the Jihadist terrorists’ communication goals of imposing a monolithic Islamic identity through a streamlined Islamic media voice. There is a decline in the Muslim support of jihadist terrorists and their deeds, particularly in countries directly affected by their indiscriminate terror attacks. This is supported by the fact that Taliban leaders held Saudi-brokered talks in Mecca between September 24 and 27, 2008 with the Afghan government to end the country’s conflict and are severing their ties with al Qaeda (Robertson 2008). Taliban leader Mullah Mohammed Omar’s representatives were keen to stress that they are no longer allied to al-Qaeda.4
7.2 Intensify the Research on the Main Communication Channel – The Internet
As this article has shown, the main communication backbone for terrorist communication is the Internet-based World Wide Web. Therefore, it must be at the center of our research. The terrorists must be combated with their own “weapons” by utilizing their main communication channel against them. In order to get a comprehensive overview, there is a need to expand primary research involving access to and interviews with terrorists as well as to broaden the systematic discussion and dissection of terrorism research. It is a primary necessity to investigate new networked communication channels (Cardoso 2008). To analyze the main jihad terrorist communication channels, a systematic, integrated approach to the study of the jihad terrorism web infrastructure—that can be visualized as hyperlinked communities—is called for. This should include automated web crawling techniques and the Dark Web Attribute System5 to study the extremist organizations’ Internet presence. Additionally, since the web based Jihadist Terrorists multimedia collections will increase, automatic extraction of structural and semantic content is an aide in the systematic analysis of the groups’ modus operandi, violent events, learning styles, networks and tactical operations. A semi-automated framework for blog analysis could be utilized to investigate the characteristic and structural relationships among the terrorist groups in blogs (Chen et al. 2008).6
7.3 Develop an International Synchronized Counter Strategic Communication Plan as Integral Element of a Comprehensive Approach
Based on these findings, and embracing the complexity of information flow, a counter strategic communication plan has to be developed and constantly adapted, to disrupt the opponents’ favorable communication asymmetry. To successfully employ a strategic counter communication plan, it has to be embedded in a comprehensive approach of coercive military7 and law enforcement measures and conciliatory political, diplomatic and socioeconomic measures. These measures and the counter communication plan have to be synchronized at all levels of government (political, diplomatic, law enforcement, military, and intelligence) and with our partners and allies, to harmonize international efforts in the global war on terror within a grand strategy (Opheim & Bowen 2008). This grand strategy, a comprehensive approach as security philosophy is an all-embracing approach that can only be developed in networked security structures based on a comprehensive international security rationale that effectively combines civilian and military instruments. Data on terrorism research should, as far as possible, be made public and shared to reduce the “hidden knowledge” in disparate databases and disconnected researchers. By internationally democratizing data and integrating both qualitative and quantitative information, we can dramatically increase our knowledge and bring greater empiricism to this field of research (Ellis 2008).
8. Conclusion
Next to developing a grand strategy to offset Jihadist Terrorists as a prerequisite, we need to focus more international research resources on countering the operational effectiveness of terrorist use of the mass media and the Internet, to undermine jihadist terrorist strategic communication operations. We need to address the root causes and hit the center of gravity, the tipping point of the Islamic society, by implanting messages and building the critical mass, cresting the threshold, when the key target audience-multipliers unleash a social epidemic in shifting views (Gladwell 2006) to turn the asymmetry in against the terrorists. Gaining a favorable communication asymmetry, is a key to hitting the opponent at their center of gravity or several conflict-determining centers in order to win the global war on terror by eliminating its root cause(s) and communicating these facts. If the jihadist terrorists’ effective strategic communication management techniques, in particular their use of the Internet, can be curtailed by a counter communication plan embedded in a grand strategy and in an internationally unified effort in all five dimensions of the battle space, the basis of their favorable asymmetry can be eroded. If jihadist terrorists can be prevented from finding new physical bases in safe havens or in ungoverned areas including the ones in the World Wide Web, global jihadism may ultimately prove to be yet another fanatical backlash, which eventually fades.
For Academic Citation
Carsten Bockstette, “Jihadist Terrorist Use of Strategic Communication Management Techniques,” Marshall Center Occasional Paper, no. 20, December 2008, https://www.marshallcenter.org/en/publications/occasional-papers/jihadist-terrorist-use-strategic-communication-management-techniques-0.
Notes
*Please note that the photos and images used in the original pdf publication are not suitable for use in html. If you would like to see the original photos, please refer to the pdf. The photos used on this website have captions giving their origins.
1 Jihad is a religious duty of Muslims. In Arabic, the word jihād is a noun meaning “struggle”. Persons engaged in jihad are called mujahideen. In this paper, the term Jihadist Terrorists describes (Al Qaida networked) terrorists that draw on extreme interpretations of Islam for their rationale, their ideology and their motivation. Their focus is not limited to any one national or ethnic milieu.
2 The Ummah, community of believers, holds its position based on the notion that it is a successor to Muhammad’s political authority. The caliphate, as the only form of governance that has full approval in traditional Islamic theology, is the core political concept that the terrorists strive to realize.
3 Lashkar-e-Taiba grew out of the 1980s resistance to the Soviet occupation of Afghanistan, has developed ties to al-Qaida. India accuses it of involvement in a string of terrorist attacks on its territory and alleges that Pakistani intelligence continues to back it—a charge vehemently denied in Islamabad.
4 The talks in Mecca took place between September 24 and 27 and involved 11 Taliban delegates, two Afghan government officials, a representative of former mujahadeen commander and Gulbadin Hekmatyar and three others. King Abdullah broke fast during the Eid al-Fitr holiday with the 17 member Afghan delegation to show his commitment to ending the conflict. The Afghan government believes the Taliban cannot be defeated militarily, and the Taliban believe that they can’t win a war against the U.S.-led coalition in Afghanistan. The involvement of the Saudi Arabia is party due to the fear that Iran could take advantage of a deteriorating security situation in Afghanistan, as Iran is seen to be doing in Iraq (Robertson 2008).
5 The Dark Web Attribute System is an integrated approach for identifying and collecting terrorist/extremist web contents. It enables quantitative Dark Web content analysis from three perspectives: technical sophistication, content richness, and web interactivity.
6 These are just a few tools to help investigate the terrorist use of the World Wide Web. For a more comprehensive look into terrorism research look at: Chen, Hsinchun & Reid, Edna & Sinai, Josua & Silke, Andrew & Ganor, Boaz (Ed.) (2008). Terrorism Informatics. Knowledge Management and Data Mining fore Homeland Security. New York: Springer.
7 On September 19, 2008 the US Department of Defense released a “Military Contribution to Cooperative Security (CS) Joint Operating Concept” Version 1.0. Although this concept is a step in the right direction, it needs to be embedded in a grand strategy, which still has to be developed at U.S.-national and international level.
About the Author
Major Dr. Carsten Bockstette is currently the Operations and German Liaison Officer in the Directors Action Group at the George C. Marshall European Center for Security Studies in Garmisch-Partenkirchen, Germany. Before he came to the Marshall Center, he served as the Commander of a PATRIOT Surface-to-Air Missile Squadron—NATO Response Force—in Sanitz, Germany from May 2005 to December 2007. Prior to this assignment, he was the Aide-de-Camp to the Commander of the German Air Force Command—Lieutenant General Walter Jertz—in Cologne. From 1998 until 2002, he served as the Tactical Control Officer and Tactical Director in the PATRIOT Surface-to-Air Missile Group in Eydelstedt, Germany. In July 1993, he joined the German Air Force and began his officer training in Fürstenfeldbruck, Germany. Major Dr. Bockstette attended the University of Texas at El Paso from January 1988 until December 1991 as well as the Helmut Schmidt University in Hamburg from October 1994 until March 1998. He holds a doctoral degree in political science from the Helmut Schmidt University in Hamburg and has been an editor and author of several publications. His published works include Strategic Information- and Communication Management (2006) and numerous publications in the areas of the media-, security-, and defensive policy. He has also contributed articles and book chapters on communication management, media work, public relations, terrorism, and asymmetric war fighting.
The George C. Marshall European Center for Security Studies
The George C. Marshall European Center for Security Studies is a leading transatlantic defense educational and security studies institution. It is bilaterally supported by the U.S. and German governments and dedicated to the creation of a more stable security environment by advancing democratic institutions and relationships, especially in the field of defense; promoting active, peaceful security cooperation; and enhancing enduring partnerships among the countries of North America, Europe, and Eurasia.
The Marshall Center Occasional Paper Series seeks to further the legacy of the Center’s namesake, General George C. Marshall, by disseminating scholarly essays that contribute to his ideal of ensuring that Europe and Eurasia are democratic, free, undivided, and at peace. Papers selected for this series are meant to identify, discuss, and influence current defense related security issues. The Marshall Center Occasional Paper Series focus is on comparative and interdisciplinary topics, including international security and democratic defense management, defense institution building, civil-military relations, strategy formulation, terrorism studies, defense planning, arms control, stability operations, peacekeeping, crisis management, regional and cooperative security. The Marshall Center Occasional Papers are written by Marshall Center faculty and staff, Marshall Center alumni, or by individual, invited contributors, and are disseminated online and in a paper version.
The views expressed in this publication are those of the author(s) and do not necessarily reflect the official policy or position of the George C. Marshall European Center for Security Studies, the U.S. Department of Defense, the German Ministry of Defense, or the U.S. and German Governments. This report is approved for public release; distribution is unlimited.